

Top 20 Linux Security Tools: Recommendation from the Linux Experts
It doesn’t matter which operating system you use, you are to utilize security software for keeping your operating system or network secured. Basically, security programs are such utilities that serve you different purposes: removal of spyware, resistance to the virus, firewall protection and many more. In short, security tools can be referred to as the blood of an operating system that destroys the harmful things just like real blood. However, there are numerous security programs, but all of those won’t function equally and properly with every operating system. Hence, here we have listed the top 20 Linux security tools predominantly for the Linux users, but if you are a user of any other operating system, you may also try.
Best Linux Security Tools
The security tools for Linux described below have been sorted out after lengthy research to provide you with the best ones with authentic information. Each of the tools contains general discussion with an impressive feature section to help you understand the potential of the tool in details.
1. MISP
MISP, elaborately known as “Malware Information Sharing Platform” is a threat intellect platform to share, store and correlate signs of the threat intelligence, economic racket information, susceptibility information, and counter-violence information. This Linux security tool is useful both for storing, sharing, collaborating cyber safety signs, malware exploration and for using the information and the IoCs for detecting and preventing the threats.

Important features
- Flexible enough to express complex objects and allied them together to reveal threat intelligence, occurrences or linked elements.
- The “intuitive user-interface” lets the end-users build, upgrade and cooperate on indicators/attributes and events.
- Stores facts in an organized layout with widespread cyber-security signs’ support.
- Combines signing and encryption of the warnings through PGP or/and MIME/S considering your preferences.
2. Privacy Badger
It is basically a privacy safeguard for browsers that provides those with security against the trackers of a website visitor. The trackers normally gather information about your browser. The collected information is frequently shared by third parties. It is often used for creating a fake profile of a specific browser. In such a case, this Linux security tool hinders the data collection.
Important features
- Runs as an extension on Opera, Firefox, and Chrome.
- Reviews the requested web-pages and deactivates those by replacing the content or simply blocking the requests.
- Disables WebRTC that reveals the inner IP addresses.
- Helps you browse the net more securely.
- Requires a little space.
3. Aircrack-ng
It is an outstanding network application suite that consists of a packet, sniffer, detector, WPA/WPA2-PSK cracker and WEP, and an analysis utility for ‘802.11’ wireless LANs. The software perfectly functions with any “wireless network interface controller” whose driver can nose 802.11g and 802.11a, 802.11b traffic and also supports the raw observing mode.

Important features
- Runs under Windows, OS X, Linux, OpenBSD, and FreeBSD.
- Its packet can seize and export data to the text-files for additional processing by the tools of the third party.
- Replays attacks, counterfeit access points, de-authentication, and other related things through packet injection.
- Checks the capabilities of the drivers and WiFi cards as well.
- Able to crack both WPA PSK and WEP.
4. Archery
Archery is a fabulous Linux security tool that helps you collect information regarding the vulnerabilities exists within your operating system. The software doesn’t only concentrate on the authentic scanning but also allows management of the findings in an interface that is essentially web-based. Here follow the outstanding features of the utility:
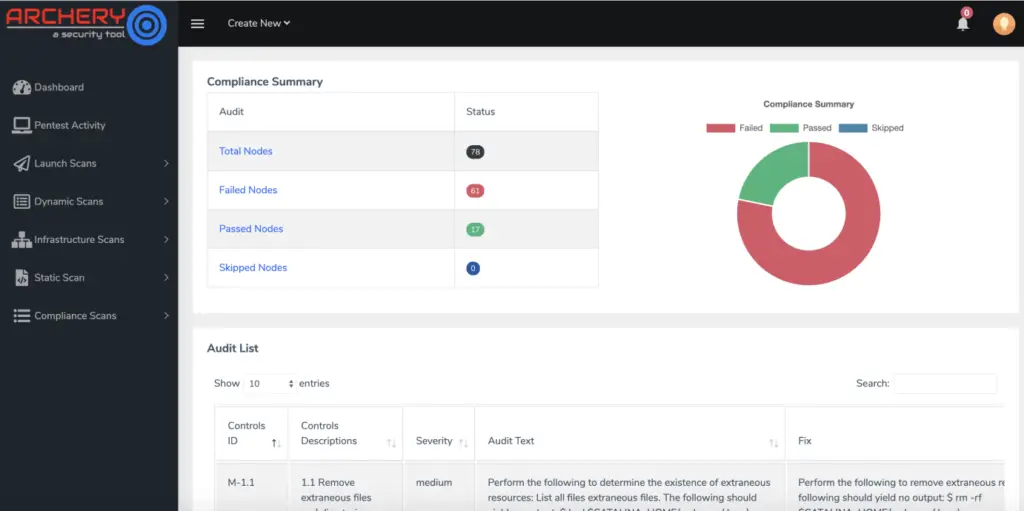
Important features
- Comprises features such as dashboards, reporting, and searching.
- Can make interaction with other applications comprising the distinguished susceptibility scanners.
- Manages scans and susceptibility in CD/CI setting for DevOps teams.
- Its assessment and managing of vulnerability are completely Open Source.
- Manages all the vulnerabilities of web-scan and discovers threats in your programs.
- Also manages all the network scans and discovers threats in the infrastructure.
5. Anchore
Anchore is such a Linux security program that can help you detect, assess and authenticate the container images. You can store the images both in the cloud and on-premises. The tool is mostly concentrated on the developers so that they can accomplish successful scrutiny on the container images. Running inquiries and producing reports are the typical activities of Anchore.
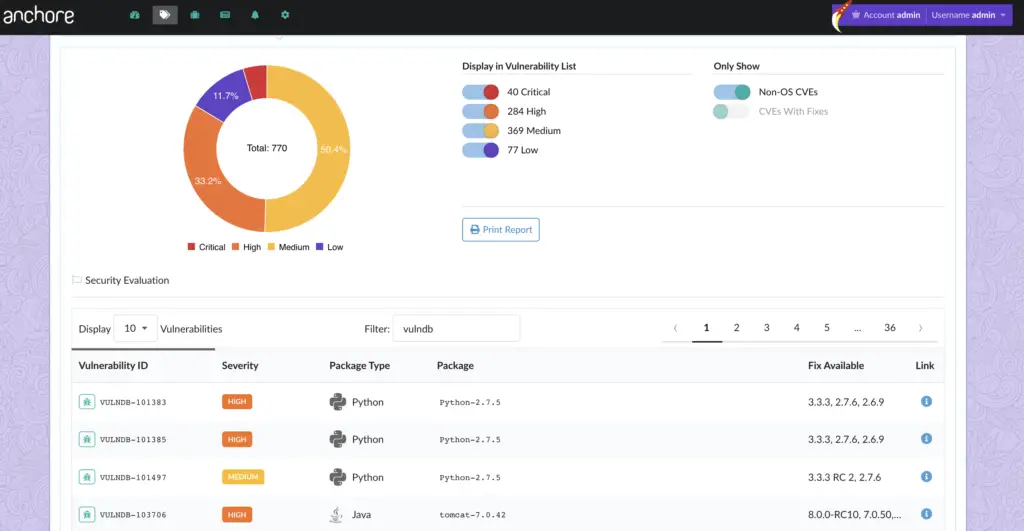
Important features
- Inspects your container images and generates a complete list of config files, Java archives, and many things more.
- Integrates with instrumentation platforms to guarantee that the images run are verified by your organization.
- Defines strategies to manage security susceptibilities, expose ports, manifest changes, and so on.
6. ClamAV
ClamAV is a standard Linux security program for detecting mischievous program or malware. Though ClamAV is known as an anti-virus engine, yet it perhaps will not come across numerous viruses because they are rare now. So, this software is more expected to discover other types of malware including ransomware, worms, and backdoors.

Important features
- You can use the tool in a number of techniques from completing a random scan-up to scanning in a group.
- Doesn’t run ‘on-access scanning’ but you can combine it with supplementary tools for obtaining alike functionality.
- Can be adapted to assist scanning the incoming emails for detecting malicious contents.
- Supports numerous signature languages and file formats, and unpacking of archive and file.
- Includes command-line utilities and a multi-threaded scanner daemon for instant scanning of files and update of signature automatically.
7. Hashcat
It is the self-declared world’s swiftest password retrieval tool that had a copyrighted code-base till 2015 and now is a completely free program. Microsoft LM hashes, Cisco PIX, MD4, MySQL, MD5, Unix Crypt formats, and SHA-family are the basic instances of hashcat supported hashing algorithms. The application comes both in GPU and CPU based variants. Its editions are compatible with Windows, Linux, and OS X.
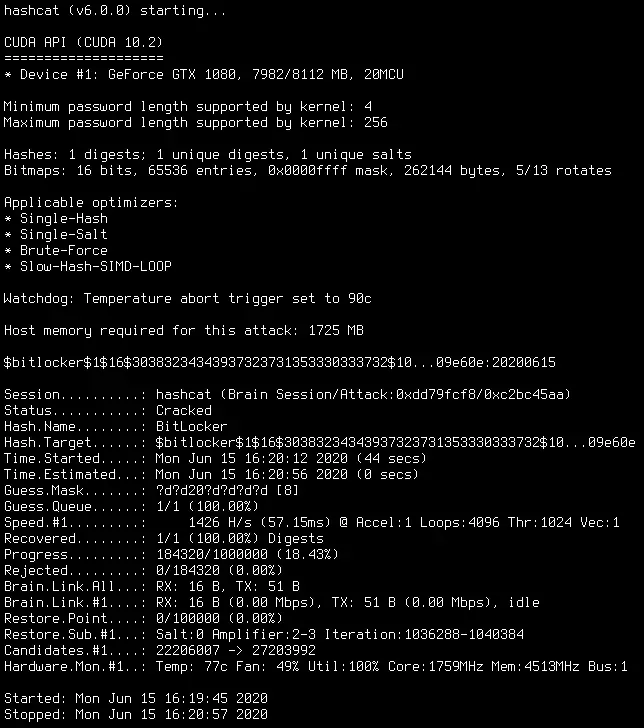
Important features
- Supports the brain functionality of a password candidate.
- Supports reading the password candidates both from stdin and file.
- Supports circulated cracking networks.
- Supports hex-charset and hex-salt.
- Supports automated keyspace ordering Markov-chains.
- Contains an inbuilt benchmarking system.
- Supports automated tuning of performance.
8. radare2
Radare2 is one of the popular Linux security tools for performing “reverse engineering” on several dissimilar file types. You can use the tool to explore firmware, malware or any other kind of ‘binary files’. In addition to “reverse engineering”, you can even use it for forensics upon filesystems and data carving. With it, you can script the tasks as well. It is capable of using software exploitation function in it.
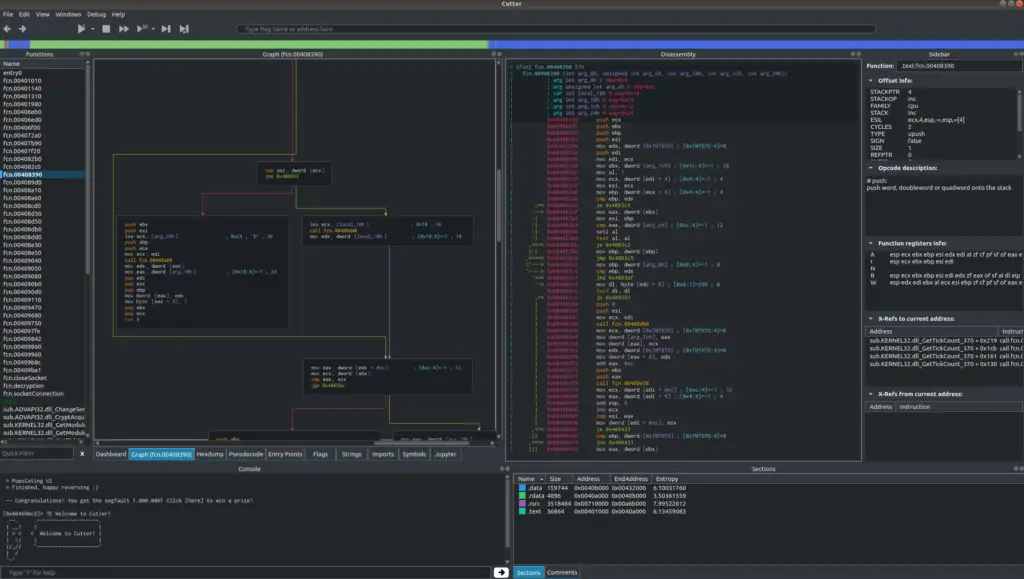
Important features
- Supports various programming languages like JavaScript, Go, and Python.
- Uses influential analysis aptitudes for speeding up the reversing.
- Visualizes data configurations of a number of file types.
- Debugs with both local and distant debuggers.
- Patches applications to expose new and exciting features or repair susceptibilities.
- Disassembles several, unlike architectures.
9. Buttercup for desktop
No, it’s not the name of any delicious dessert that we are going to present to convince you to eat. Instead, it is a mind-blowing password manager that is intended to help you control your credentials. A powerful encryption is used by it for guarding your sensitive files and materials under only one master password.
Important features
- Allows you to use more difficult passwords for individual service and stores those securely.
- You can install it directly on Google Chrome while on Mozilla Firefox the tool is found as an extension.
- Includes simple to use interface where saving and finding the details of login is easier
- Completely free to use on all the key platforms.
- Serves equally both on Android and Ios mobile phones.
10. Bro
“Bro” helps you extensively perform the monitoring of security looking into the activities of the network. This Linux security utility is able to identify the doubtful data streams. Considering the data, the program alerts reacts, and even integrates with other related tools. This fabulous software has been advanced by Vern Paxson who now leads the project with a potential group of scholars and developers.
Important features
- Its domain-based scripting language facilitates site-specific observing strategies.
- Aims at high-performance networks.
- Not bound to any specific discovery tactic and doesn’t depend on outdated signatures.
- Expansively records what it finds and offers a high-level store of the activities of a network.
- Interfaces with other programs for the give-and-take of information in real-time.
- Maintains far-reaching program-layer state regarding the network it observes.
11. Faraday
Faraday is a real-time cooperative utility that upsurges velocity, efficiency, and transparency for your and your teams’ assessments. This Linux security tool provides you with superior perceptibility and helps make cooler safekeeping investment. The software serves many organizations all over the world. It is even able to meet the requirements of different organizations offering appropriate solutions to each case.
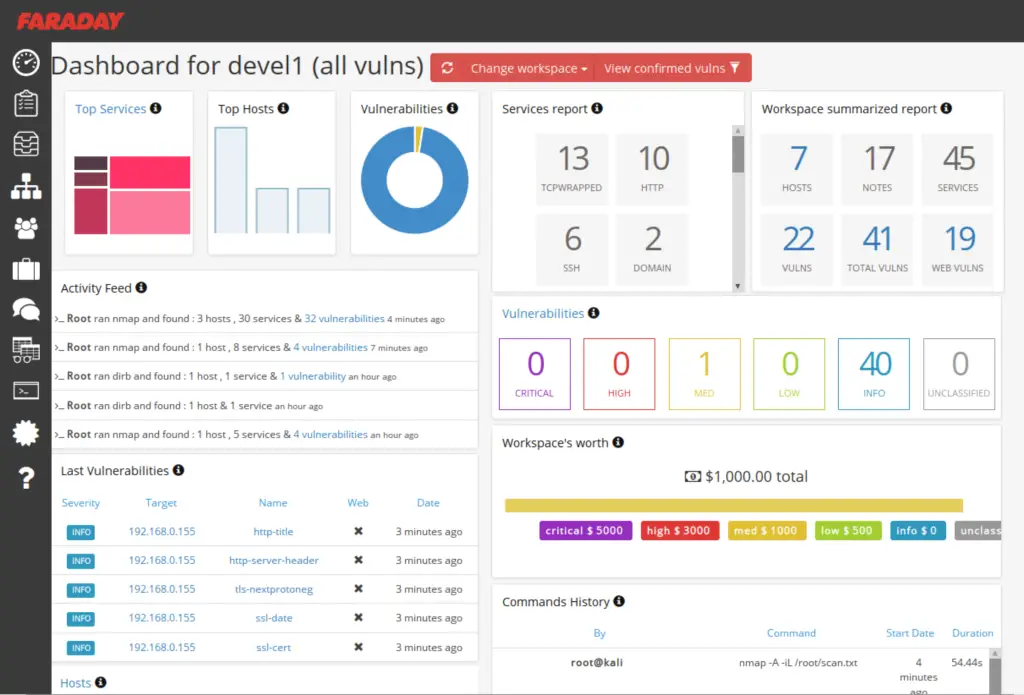
Important features
- Equipped with simplicity with a particular set of functional activities that help you develop accomplishing your work.
- As a user, you have the opportunity for generating a timeline that contains each historical modification within the existing penetration investigation.
- Gives the opportunity for making a comparison of two, unlike pentests.
- Enables the corporates, penetration testers, and project managers to have a real-time view of the work in development.
12. Frida
Another great Linux security framework- “Frida” lets the researchers and developers inoculate ‘custom scripts’ into ‘black box methods’. In this way, the tool provides all the functions with a hook, letting you trace the performed instructions. It even approves uninterrupted manipulation and observes the outcomes.
Important features
- You can get Frida with available bindings for various programming languages that allow relating to processes.
- Doesn’t require any source code for tracing personal application code and hooking functions.
- Allows you to edit, store, and examine the outcomes.
- Contains a complete test-suite.
- Available options for personalization and addition.
- Compatible with QNX, Windows, GNU/Linux, Android, macOS, and iOS.
13. PTF
PTF, the short form of or “PenTesters Framework” is a Python script that aims at keeping your penetration analysis toolkit latest. It is an excellent Linux security program that is intended to run under Ubuntu, Arch Linux, Debian, or associated clones. It basically functions with modules where you get the definition of the method of fetching a tool and an overview of the needed things for building the tool.
Important features
- Capable of retrieving, compiling, and installing the tools normally used by you.
- The tool is a modular structure; you are allowed to utilize lots of typical pen-testing tools and attach your own utilities.
- Makes sure that each and everything is structured according to the “Penetration Testing Execution Standard.”
14. Intrigue
It is one of the finest Linux security utilities that is extensively used to discover the attack surface. The discovery relates to applications and infrastructure, vulnerability, and security research.
Important features
- Includes a bunch of scripts to sort out the required information.
- Provides unmatched visibility of external asset.
- Identifies the uncovered susceptibilities in the program stacks and their core hosts.
- Lets you export vulnerability information for the management teams.
- Helps the security teams gain perceptibility of the third party risk.
- Allows you to enrich the existing data and carry out OSINT exploration.
- Enables security teams to identify the un-used assets that still pose a threat to the company.
15. Vault
It is a fantastic secret management program made by HashiCorp that is an expert in preserving your invaluable data. The secrets stored by it are normally utilized by software scripts and components. Vault employs an API to let you have access to the encoded secrets. The confidential issues themselves can either be prevalent or dynamically created.
Important features
- Allows storing confidential things including STS/ AWS IAM credentials, value/key pairs, NoSQL/ SQL databases, SSH credentials, X.509 certificates, and many other sensitive details.
- Includes leasing, auditing, key rolling, and key revocation.
- Offers encryption just like a service with ‘integrated key management.’
- Simplifies the encryption of data both at rest and in transit across data centers and clouds.
16. CAIRIS
CAIRIS, an outstanding Linux security framework basically stands for “Computer Aided Integration of Requirements and Information Security.” It is such a great platform that with it you can elicit, specify, and validate the functioning systems. The tool was created to support each element required for analysis of risk, usability, and requirements.
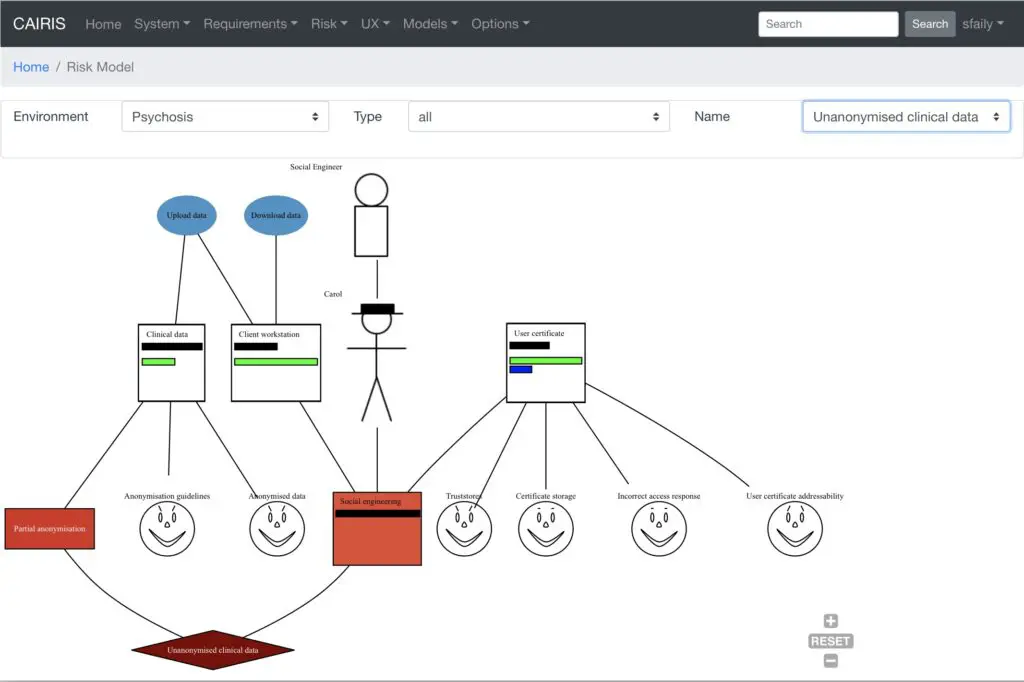
Important features
- Allows you to create a safeguard for software and designing of the system.
- Lets you track the communications between data points, objects, and associated risks.
- Automatically generates threat models like “Data Flow Diagrams” as soon as your design of primary phase evolves.
- Produces a series of papers from “Volere compliant requirement specifications” to “GDPR DPIA documents”.
- Leverages not only open source brain about probable attacks but also candidate safeguard architectures for measuring the attack surface.
17. O-Saft
It is one of those rare command-line tools that you can use both in closed settings and offline. The Linux security application contains a Tk/Tcl based graphical user interface. Besides, you can turn it into an online CGI-utility.
Important features
- Provides convenient SSL configuration information with its elementary parameters.
- Performs more particular tests with limited tool tuning.
- Allows you to gather information, test penetration, assess security, scan vulnerability, or analysis of web application.
- Supports STARTTLS for different types of protocols including SMTP, IRC, POP3, XMPP, IMAP, RDP, LDAP.
- Checks for securities against some attacks such as BEAST, FREAK, DROWN, CRIME, and so on.
- Shows the details of certificate and SSL connection.
18. YARA
YARA is another fabulous Linux security utility that is intended to assisting the malware scholars to recognize and categorize the malware samples without any limitation. With this framework, you can easily produce descriptions of the malware families or anything else according to your desire grounded on binary or textual patterns. All the descriptions, which are also known as rules, consisting of a boolean expression and a bunch of strings.
Important features
- Lets you create more compound and influential rules using case-insensitive strings, wild-cards, special operators, regular expressions, and several other features.
- Equally runs on Linux, Mac OS X, and Windows.
- You can use it from your personal “Python scripts” with an extension of Yara-python or via YARA’s command-line interface.
19. OpenSSL
This is a marvelous software library, which is suitable for the applications that you use to protect interactions over the computer networks against overhearing. The central library is written using the C programming language. This Linux security utility is extensively adopted in the web servers of the Internet, and now a majority of the websites is served by it.
Important features
- Includes an open source execution of the TLS and SSL protocols.
- The core library can execute fundamental cryptographic tasks and provide different tool functions.
- Wrappers are available that allow you to use the OpenSSL library with multiple computer languages.
- Editions are compatible with Windows, OpenVMS, and most Unix and Unix-like operating systems including Linux, Solaris, QNX, macOS, etc.
20. Confidant
Confidant, popularly known as “storage of secrets” provides you with a substitute by preserving you confidential facts in a database instead of a configuration file. The tool functions in such a way that it doesn’t give access to all applications to have the facts. Even often the system managers are not given access if anything dubious is captured by Confidant.
Important features
- Solves the verification egg and chicken problem using IAM and AWS KMS.
- Stores your confidential files in an append-only method creating an exclusive KMS data-key for the revisions of all the secrets.
- Provides an “AngularJS web interface” that lets the end-users manage the secrets and their mappings very easily.
Finally
So, this is all about the “Linux Security Tools.” We are optimistic that this piece of software and tools compilation will help you to set up a secured OS. However, please let us know your opinion regarding our writing through a comment below so that we can come to know of your expectations from us and act accordingly next time. And yes, most importantly, don’t forget to share the writing to escalate our inspiration needed to bring betterment.




























Leave a Reply