
Top Free Vulnerability Assessment Tools

The Top Free Vulnerability Assessment Tools
by Andrew Scott
If you’re looking to learn more about vulnerability scanners on the cheap, look no further
Whether you’re a student, studying for certification, or a vulnerability management pro, finding cheap tools to satisfy educational requirements or satiate your scanning curiosity can be difficult. In this post I’ll be looking at my top 5 free vulnerability assessment tools.
Network Scanning vs. Vulnerability Assessment vs. Vulnerability Management
This terminology can get a little confusing. Network Scanning can often be boiled down to the act of port scanning and mapping a network. Vulnerability Assessment is one step beyond network scanning where there is an additional step to identify services and test for vulnerable software. Finally Vulnerability Management is the process of identifying, prioritizing, and remediation vulnerabilities detected in a network. The primary focus here will be on the first two, as true Vulnerability Management solutions are generally too complex to be offered as a free standalone tool.
Comparison Criteria
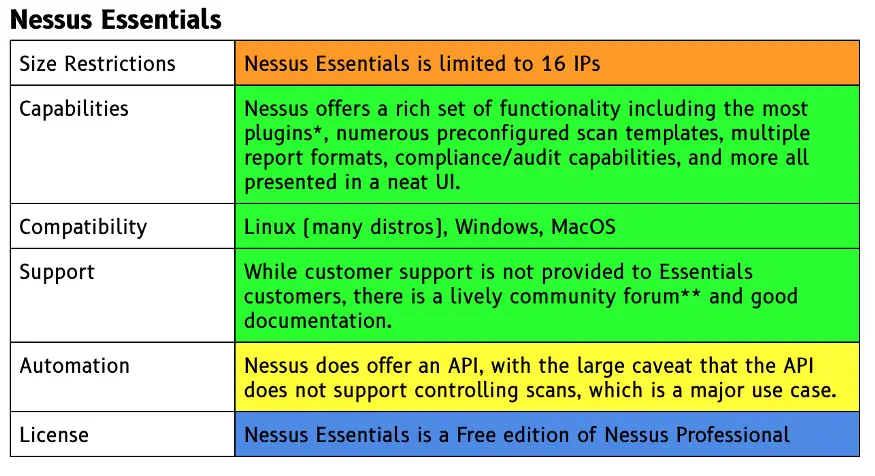
Size Restrictions
Some of these free tools come to us in the form of community editions of a company’s commercial product. One common way these CE versions of the tool are limited is how many IPs or assets they can analyze. Obviously if this count is smaller than the number of hosts on your network it can be a real downside.
Capabilities
Not all tools are created equal when it comes to functionality, some are much more feature rich and others are bare-bones workhorses. It bares keeping in mind what capabilities are most important to you when selecting a tool as there will always be tradeoffs.
Compatibility
Every environment is different and flexibility in where and how the tool can be deployed is key.
Support
All of the tools here include different levels or support either from a company or an open source community. While these things can be difficult to gauge — looking at qualitative measures like the number of open issues on a github project or how lively the community forum are can be indicators.
Automation
Being that one of the primary parts of my day job is how to automate wide arrays of security tools into a cohesive (hopefully elegant) solutions, looking at how easily a tool can be automated is a facet I’m always looking for.
License
Here I’ll just enumerate whether the tool is totally open-source, or whether it’s a free version of a commercial product.
Exclusions
I’ve excluded any Vulnerability Assessment or Scanner tools that are only free during a limited license period. While these are technically free, I’d argue that they should really only be considered for use with the purpose of actually testing out the paid version of the product. I’d also caution against using this class of tools if you just need the tool for a limited period of time or single use — unless you’re already intimately familiar with the trial tool you’ll probably be spending more time overcoming the learning curve of each tool than getting good results.
The unpaid versions of these tools also often lack functionality that is included in the paid version of the tool — so if you’re hunting for a specific feature you may not actually be able to demo that in a trial version.
A notable examples of a capable Network Scanning/VM tools that offers a 30 day trial is Rapid7’s InsightVM.
I’ve also excluded tools that are primarily focused on Web Application Scanning. Web App Scanning (WAS) is certainly part of Vulnerability Assessment and Vulnerability Management, but it takes a much more narrow approach than the other tools I’ve included.
Some examples of Free WAS tools I’ve excluded are Nikto, Arachni, and OWASP Zed Attack Proxy (ZAP).
Top 5
Nessus Essentials
In the world of Vulnerability Assessment tools, Tenable’s Nessus is an undisputed leader. Nessus was started in 1998 by Renaud Deraison. In 2005 Nessus was changed from an Open Source project to Closed Source and offered as a product by Tenable. Today Nessus lives on as Nessus Essentials (free) and Nessus Professional (commercial) and Deraison continues to be involved as Tenable’s CTO driving the research that makes its way into Nessus in the form on Plugins. To date Tenable has published nearly 150,000 plugins.
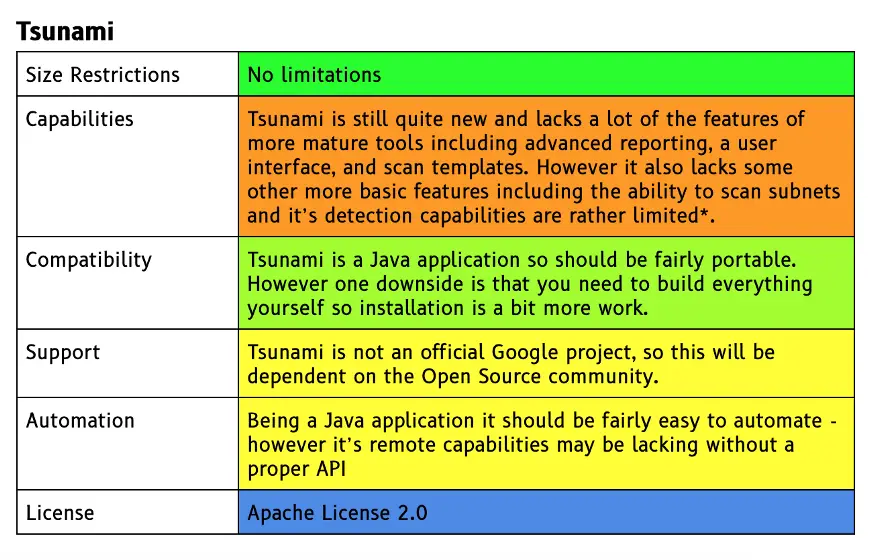
Tsunami Security Scanner
Unlike Nessus which which is now older than many new security students, Tsunami Security Scanner is fresh on the scene in 2020. Tsunami is notable for a few reasons, not least of which that it was formerly an internal project for scanning large enterprise networks within Google, but it’s also the newest product on this list, with most of the others being at least a decade old.
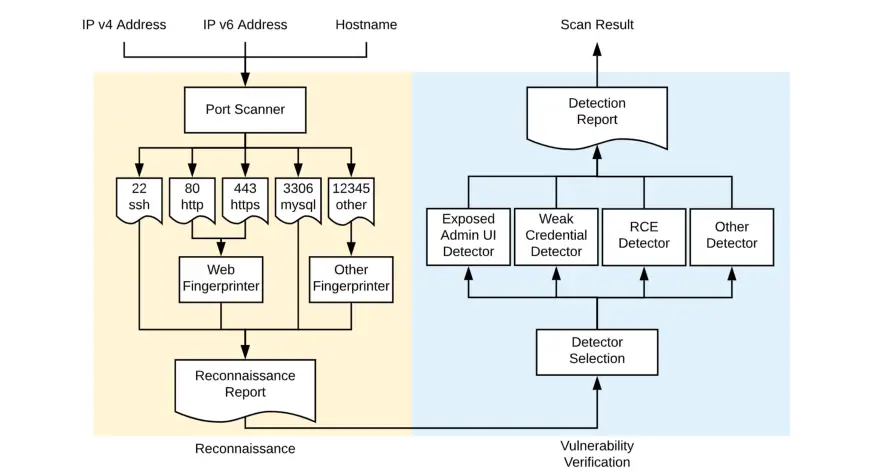
Under the hood, Tsunami actually makes use of Nmap for doing to actual post scanning during its reconnaissance phase, before doing fingerprinting then executing a number of vulnerability detection plugins against its findings.
While the project has gotten some press recently and has the benefit of greenfield development, it does lack the battle-tested reassurance of the other products on this list and it remains to be seen how it will be adopted.
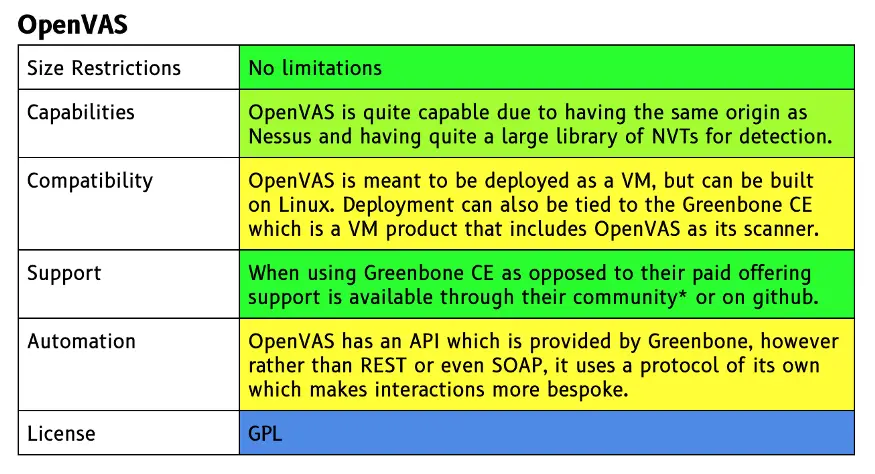
OpenVAS
OpenVAS is a vulnerability assessment tool that that actually shares its history with another product on this list, Nessus. It was forked from Nessus back in 2005 as Nessus was transitioning from an Open Source project to a privately managed commercial tool. OpenVAS’ scan engine is updated daily by Greenbone via the Greenbone Community Feed (GBF) with new network vulnerability tests (NVTs) to detect newly publicized vulnerabilities. There are currently over 50,000 NVTs. OpenVAS is most often used within the context of Greenbone Community Edition (CE) or Greenbone Security Manager.
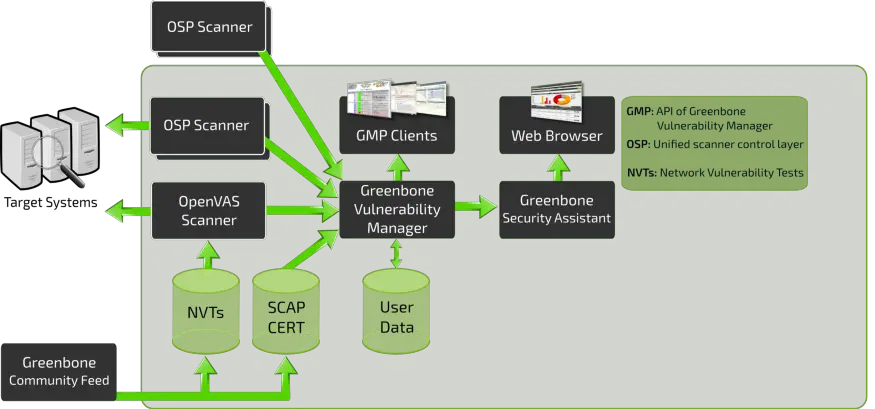
OpenVAS – Open Vulnerability Assessment Scanner
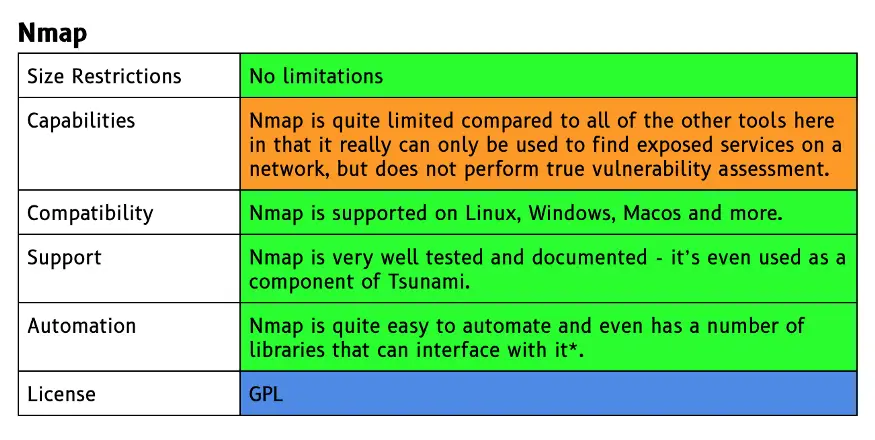
Nmap
Nmap is THE quintessential network scanning tool. I hesitated whether to include Nmap because of all of the tools listed it’s both the least capable for pure Vulnerability Assessment and also one of the most recognized security tools and ancestral scanning tools (See Tsunami above, and Zmap).
Nmap was first published in 1996, making it the oldest tool on this list. It includes a GUI with the addition of Zenmap, but is most commonly used as a command line tool.
Unlike the other tools on this list Nmap does not do vulnerability checks, it is merely a port scanner, meaning it can find exposed services, but does not contain the actual checks to verify whether an exposed service has a known vulnerability.
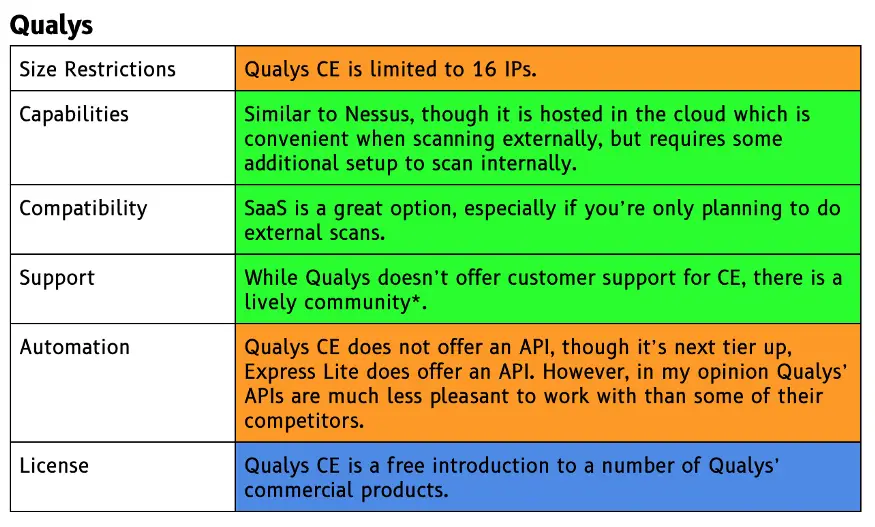
Qualys Community Edition
Not to be outdone by Tenable, Qualys also has a Free edition of their own Vulnerability Management software. The primary differentiator between Qualys CE and Tenable Essentials is that Qualys CE is a SaaS product, meaning that there’s nothing to download or install if you plan to scan externally.
Qualys CE also allows you to scan a single Web Application, which is an additional capability that is nice to see and is lacking from all of the other tools on this list, making it perhaps the most flexible tool here.
If I were to chose a product from this list and only needed to ever scan a few hosts on my home network or in a lab, Nessus Essentials would be my choice. It’s simple to install and get started with and provides a ton of great features; plus the Tenable research team is second to none in the VM world.
If I needed to actually use one of these tools in practice and had absolutely 0 budget I would stick with OpenVAS as Nmap is too incomplete and Tsunami is still too immature. What do you think? Are there any free tools I missed that you’re having success with?


























Leave a Reply