
You are a Threat Hunter. While investigating, did you find yourself with more than 20 tabs opened in your browser, scattered .txt files with data and some terminals showing up in the background? theTHE centralizes all the information on an investigation in a single project and shares its results with your team (and with nobody else). theTHE caches your API responses, so you don’t need to repeat the requests. Don’t share your keys, let the users make calls to the services. theTHE also contains some command-line tools integrated so you don’t have to open a terminal and pipe the results in a .txt file.
Your feedback is welcome.
TheTHE is an environment intended to help analysts and hunters over the early stages of their work in an easier, unified and quicker way. One of the major drawbacks when dealing with a hunting is the collection of information available on a high number of sources, both public and private.
All this information is usually scattered and sometimes even volatile. Perhaps at a certain point there is no information on a particular IOC (Indicator of Compromise), but that situation may change within a few hours and become crucial for the investigation. Based on our experience on Threat Hunting, we have created a free and open source framework to make the early stages of the investigation simpler from:
- Server-client architecture. Investigation may be shared among your team.
- APIkeys are stored in a database and may be shared by a team from a single point.
- Results are cached; so not repeated API calls are used.
- Better feeds your Threat Intelligence Platform. TheTHE allows to better perform a prior investigation of your assets.
- Easy plugins: Whatever you need, it is easily embedded within the system.
- Ideal for SOCs, CERTS or any team.
- Automation of tasks and searches.
- Rapid API processing of multiple tools.
- Unification of information in a single interface, so that screenshots, spreadsheets, text files, etc. are not scattered.
- Enrichment of collected data.
- Periodic monitoring of a given IOC in case new information or related movements appear.
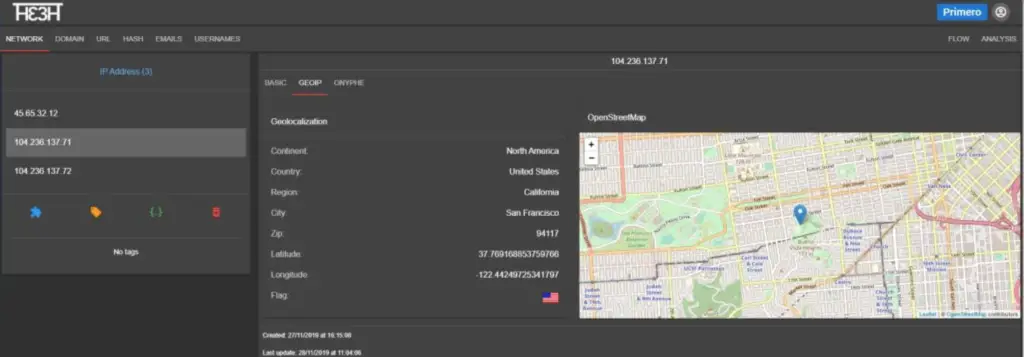
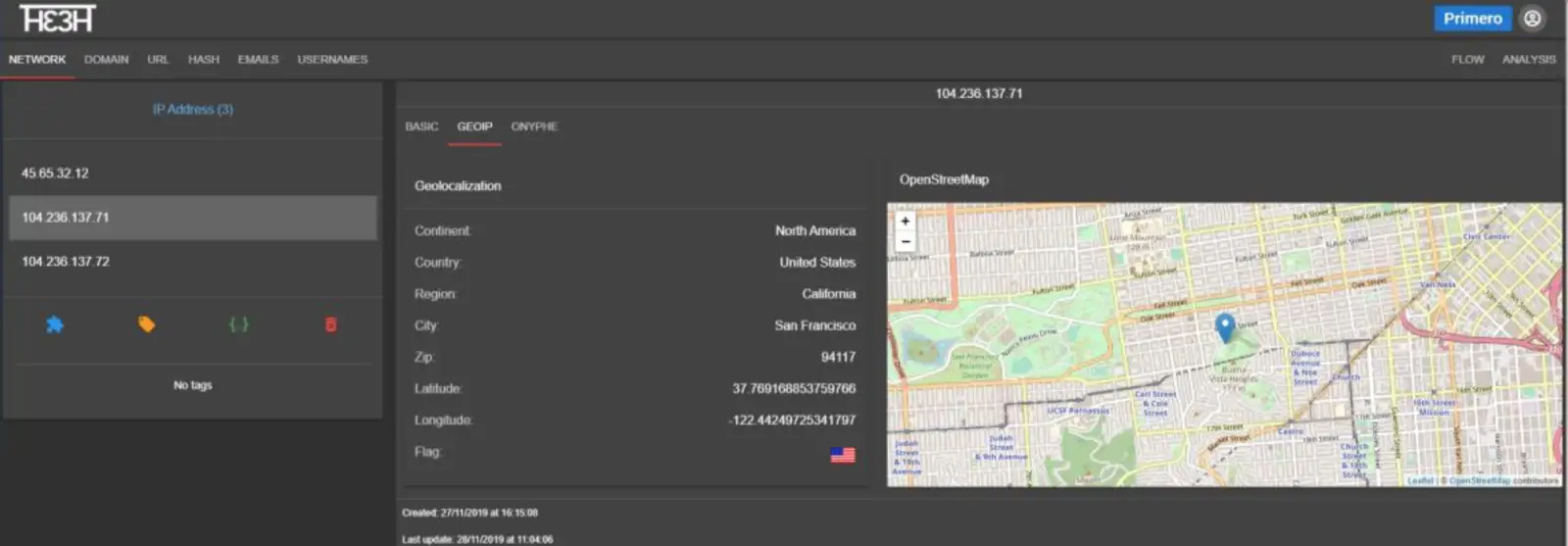
TheTHE has a web interface where the analyst starts its work by entering IOCs that will be sent to a backend, where the system will automatically look up for such resource on the various configured platforms in order to obtain unified information from different sources and access related reports or data existing on them. Furthermore, any change in the resources to be analyzed will be monitored.
Everything is executed on a local system, without needing to share information with third parties until such information is not organized, linked, complete and synthesized. This allows that, in case the information must be analyzed later on any other platform (such as a Threat Intelligence Platform), it can be done in the most enriching possible manner.
Installation
First, clone this repository with:
git clone https://github.com/ElevenPaths/thethe.git
Last, build the images and run the containers
docker-compose up -d
You should see thethe in http:// localhost after a ☕️
Default user
By default, there is only one user admin with password admin
Change the admin password as soon as you login into thethe the very first time.
API keys
There are not API keys stored by default in the system.
To add an API key, there is an option in the user menu (right upper corner).
All API keys (a new API management system is in development) must be written as CSV values:
service_name_1,api_value_1
service_name_2,api_value_2
...
service_name_n,api_value_n
What if a service must have more than one API key, secret, etc…
secret,api_value
...
cookie,cookie_value
Database backups and restoration
Mongodb has a bind volume to ease external storage and backups in a folder mongodb_data
In any case, we have provided you a couple of scripts to backup (a compressed file) and restore data from your mongo container.
Inside utils folder:
Make a backup
backup_thethe_db.sh
Restore from a backup
restore_thethe_db.sh
Updating
Make a database backup! (look section “Database backups and restoration”)
git pull
If the source code has been changed all the mounted volumes should reflect the changes, but in certain cases (third party libraries, etc) the images must be rebuilt.
Stop the containers:
docker-compose stop
Rebuild images:
docker-compose build
Restart the system
docker-compose up -d
Development environment
If you want to collaborate with the project a development version is provided:
Get the repository
git clone https://github.com/ElevenPaths/thethe.git
Docker (don’t forget your ☕️)
docker-compose -f docker-compose_dev.yml up -d
Run the frontend
cd frontend
npm install
npm run serve
























Leave a Reply