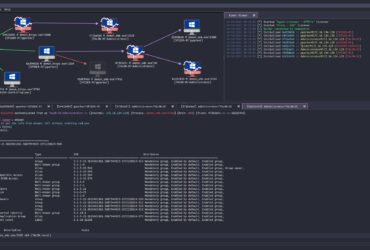
The Havoc Framework Havoc is a modern and malleable post-exploitation command ...
OSCP Cheat Sheet Commands, Payloads and Resources for the Offensive Security ...
backvenom multi-purpose Red Team Assessment access and exploitation framework for exploitation ...
Awesome Bloodhound A curated list of awesome Bloodhound resources This list ...
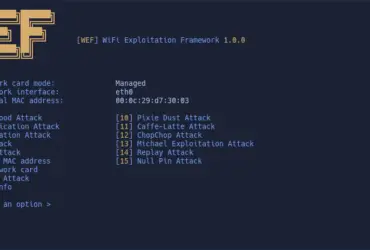
WEF – WiFi Exploitation Framework A fully offensive framework to the ...
Advanced Windows exploit development resources Some resources, links, books, and papers ...
A curated list of various bug bounty tools Recon Subdomain Enumeration ...
Automatic Linux privesc via exploitation of low-hanging fruit e.g. gtfobins, pwnkit, ...
A toolkit that brings together penetration testing tools such as wireless ...
CVE-2022-24086 about Magento RCE Description Adobe Commerce versions 2.4.3-p1 (and earlier) ...