

MagicRecon: Fast, simple and effective
Hi hacker
Welcome to the MagicRecon tool repository!
MagicRecon is a powerful shell script to maximize the recon and data collection process of an objective and finding common vulnerabilities, all this saving the results obtained in an organized way in directories and with various formats.
With Magic Recon you can perform passive and active reconnaissance, vulnerability analysis, subdomain scan and many more!
Disclaimer
The author of this document take no responsibility for correctness. This project is merely here to help guide security researchers towards determining whether something is vulnerable or not, but does not guarantee accuracy. Warning: This code was originally created for personal use, it generates a substantial amount of traffic, please use with caution.
Main features
- Save the results in an organized way in different formats.
- Subdomain enumeration.
- Check if the domains are alive.
- Get whois information about every subdomain.
- Get dns information about every subdomain.
- Extract the technologies used in the domain.
- Get information about the certificate used in the domain .
- Take a screenshot on the domain.
- Searches for emails on the domain, users and more things.
- Enumerate public resources in AWS, Azure, and Google Cloud.
- Search juicy information via GitHub Dorks.
- Check all entrys in robots.txt file.
- Get all endpoints on the web.
- Perform a parameter scan.
- Perform a port scan to discover open ports.
- Perform a dirsearch to find directories and files.
- Check if is possible to bypass 403 HTTP status code.
- Perform a massive recon and vulnerability scan via Nuclei every X seconds.
- Search missing security headers.
- Check if the domain is vulnerable to Email spoofing.
- Check if the domain is vulnerable to Subdomain takeover.
- Check if the domain is vulnerable to Cross-Origin Resource Sharing (CORS).
- Check if different endpoints are vulnerable to CSRF.
- Look for entry points in the URL and check if it is vulnerable to Open Redirect.
- Look for entry points in the URL and check if it is vulnerable to Cross-site scripting (XSS).
- Look for entry points in the URL and check if it is vulnerable to SQL Injection (SQLi).
- Look for entry points in the URL and check if it is vulnerable to Server-side request forgery (SSRF).
- Search all JS files in the domain and perform a scan for API Keys, access tokens, endpoints, etc.
- Check if the domain use a CMS and scan it.
- And many more…
Installation
$ git clone https://github.com/robotshell/magicRecon
$ cd magicRecon
$ chmod +x install.sh
$ ./install.sh
Configuration
To configure MagicRecon tool you must open the configuration.cfg file and change variables defined by user data.
It is also important to correctly configure tools such as Subfinder and Notify to guarantee the correct functioning of magicRecon.
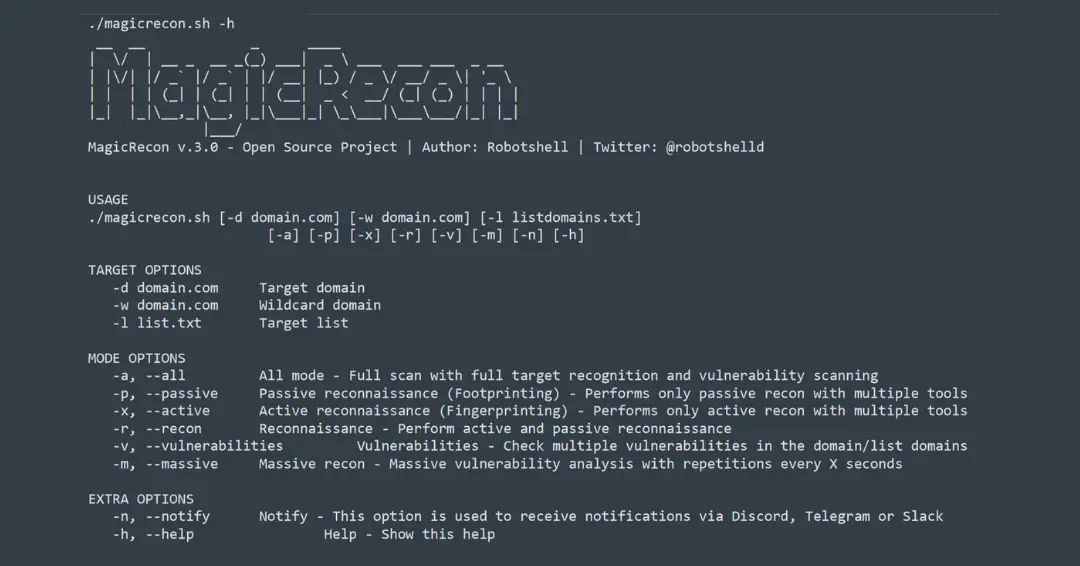
Usage
TARGET OPTIONS
| Parameter | Description |
|---|---|
| -d | Target domain |
| -w | Wildcard domain |
| -l | Target list |
MODE OPTIONS
| Parameter | Description |
|---|---|
| -a, –all | All mode – Full scan with full target recognition and vulnerability scanning |
| -p, –passive | Passive reconnaissance (Footprinting) – Performs only passive recon with multiple tools |
| -x, –active | Active reconnaissance (Fingerprinting) – Performs only active recon with multiple tools |
| -r, –recon | Reconnaissance – Perform active and passive reconnaissance |
| -v, –vulnerabilities | Vulnerabilities – Check multiple vulnerabilities in the domain/list domains |
| -m, –massive | Massive recon – Massive vulnerability analysis with repetitions every X seconds |
EXTRA OPTIONS
| Parameter | Description |
|---|---|
| -n, –notify | Notify – This option is used to receive notifications via Discord, Telegram or Slack |
| -h, –help | Help – Show help |
./magicrecon.sh -h
__ __ _ ____
| \/ | __ _ __ _(_) ___| _ \ ___ ___ ___ _ __
| |\/| |/ _` |/ _` | |/ __| |_) / _ \/ __/ _ \| '_ \
| | | | (_| | (_| | | (__| _ < __/ (_| (_) | | | |
|_| |_|\__,_|\__, |_|\___|_| \_\___|\___\___/|_| |_|
|___/
MagicRecon v.3.0 - Open Source Project | Author: Robotshell | Twitter: @robotshelld
USAGE
./magicrecon.sh [-d domain.com] [-w domain.com] [-l listdomains.txt]
[-a] [-p] [-x] [-r] [-v] [-m] [-n] [-h]
TARGET OPTIONS
-d domain.com Target domain
-w domain.com Wildcard domain
-l list.txt Target list
MODE OPTIONS
-a, --all All mode - Full scan with full target recognition and vulnerability scanning
-p, --passive Passive reconnaissance (Footprinting) - Performs only passive recon with multiple tools
-x, --active Active reconnaissance (Fingerprinting) - Performs only active recon with multiple tools
-r, --recon Reconnaissance - Perform active and passive reconnaissance
-v, --vulnerabilities Vulnerabilities - Check multiple vulnerabilities in the domain/list domains
-m, --massive Massive recon - Massive vulnerability analysis with repetitions every X seconds
EXTRA OPTIONS
-n, --notify Notify - This option is used to receive notifications via Discord, Telegram or Slack
-h, --help Help - Show this help
Example Usage
All:
./magicrecon.sh -d domain.com -a
Passive reconnaissance to a list of domains:
./magicrecon.sh -l domainlist.txt -p
Active reconnaissance to a domain:
./magicrecon.sh -d domain.com -x
Full reconnaissance:
./magicrecon.sh -d domain.com -r
Full reconnaissance and vulnerabilities scanning:
./magicrecon.sh -d domain.com -r -v
Full reconnaissance and vulnerabilities scanning to a wildcard:
./magicrecon.sh -w domain.com
Massive reconnaissance and vulnerabilities scanning:
./magicrecon.sh -w domain.com -m
Sample video: passive reconnaissance
To do
- Change tool operation to parameters.
- Improve the use of Notify.
- Add new interesting tools to find more vulnerabilities.
- Save results in other formats.
- Save the results in a document as a report.
- Check if the emails found by the tool are leaked.
- Integrate RobotScraper.
Contribution & License
You can contribute in following ways:
- Report bugs & add issues.
- Fix something and open a pull request.
- Give suggestions (Ideas) to make it better.
- Spread the word.
Do you want to have a conversation in private? email me : robotshelld@gmail.com
MagicRecon is licensed under GPL-3.0 License
Special thanks
- Special Thanks to Mohd Shibli for his great contributions in the article Fasten your Recon process using Shell Scripting
- Special Thanks to @KingOfBugbounty for his great contributions in the repository KingOfBugBountyTips
- @TomNomNom
- @pdiscoveryio
- @NahamSec
- @s0md3v
- @ofjaaah
- @KingOfBugbounty
About me
https://twitter.com/robotshelld
Useful?
- If you’ve earned a bug bounty using this tool, please consider donating to support it’s development. You can help me to develop more useful scripts and tools. Thanks!

























Leave a Reply