
SECMON – Infosec Watching Tool
Description
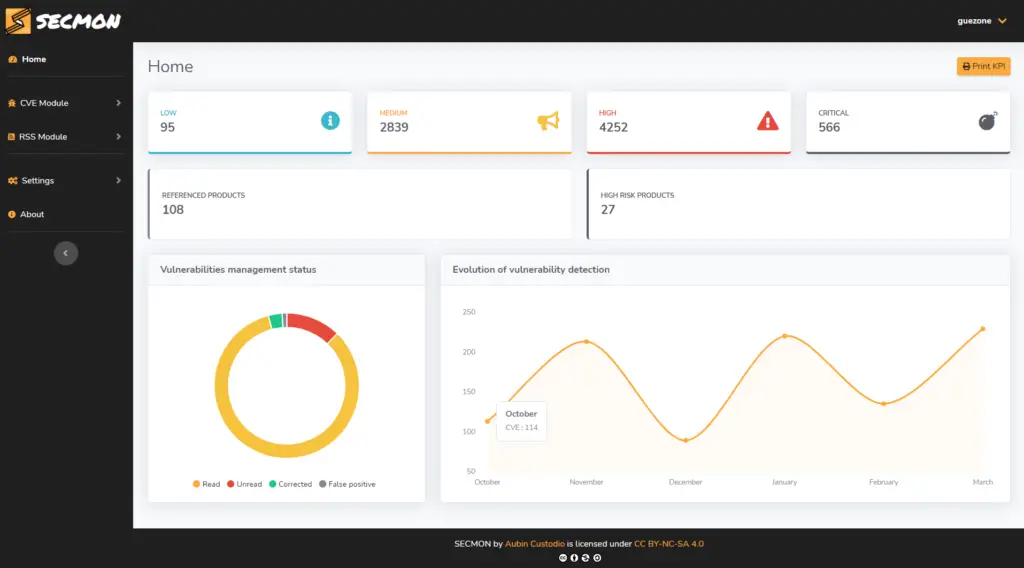
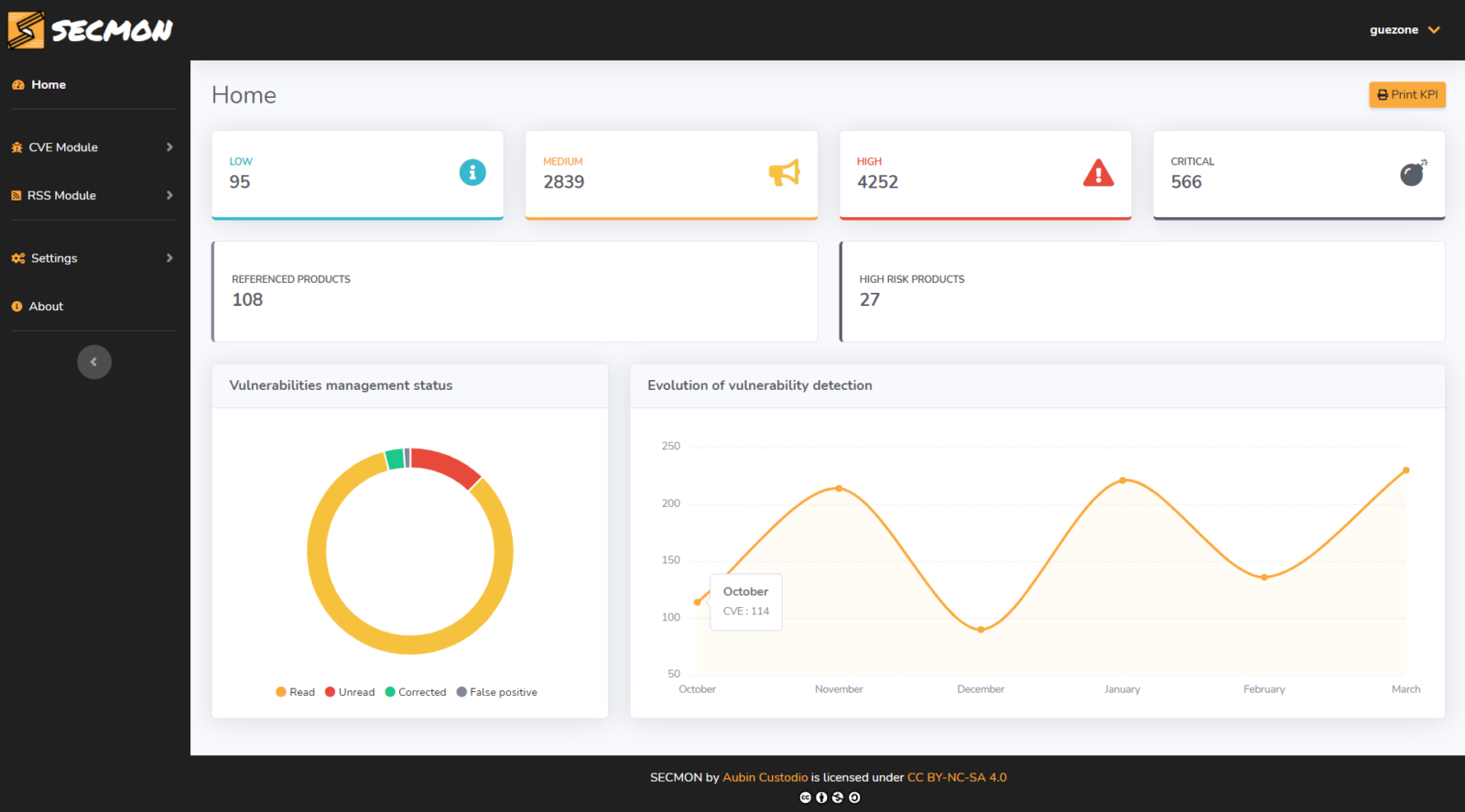
SECMON is a web-based tool for the automation of infosec watching and vulnerability management with a web interface.
A demo And discord channel is available
https://secmon.guezone.info/
https://discord.gg/cXzvb4fKzE
Features
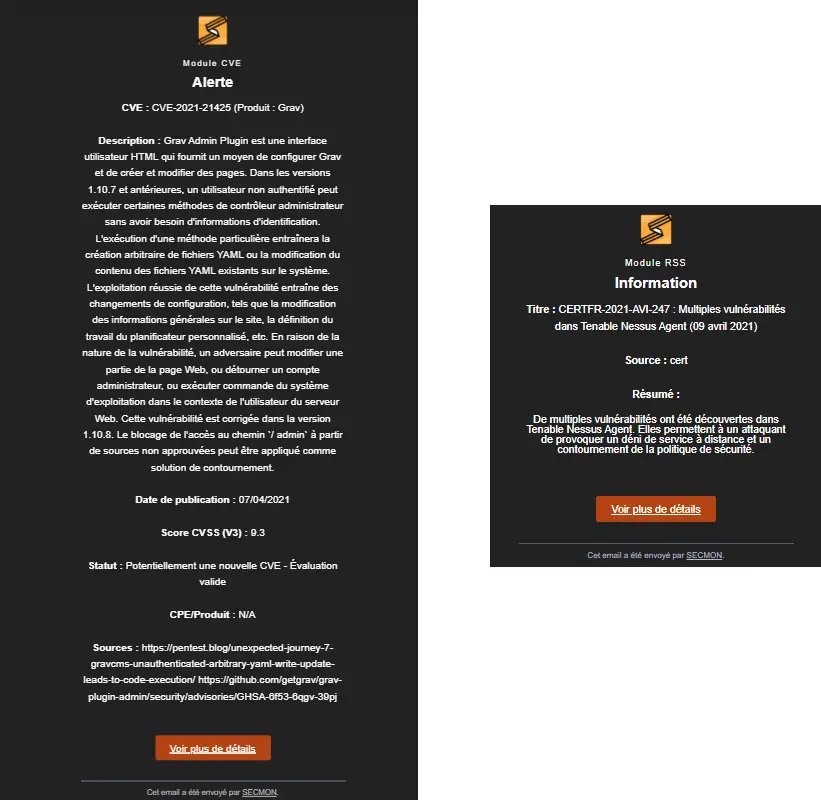
- Mail alerting when a new CVE is published and which concerns your product list
- Mail alerting when a “cyber-security” news are published: new threats, recent attacks, events, etc.
- Visualize the high security risk products present on your IT infrastructure
- Download CVE Excel report by date range
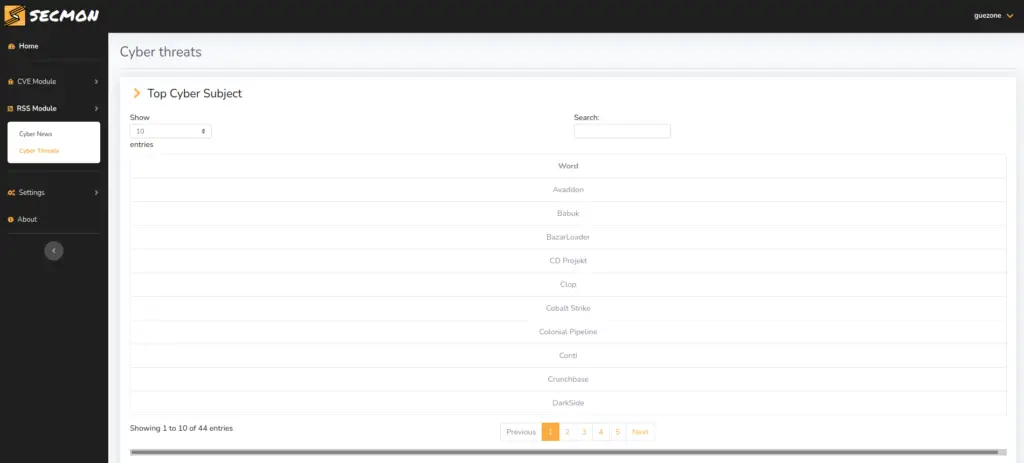
- Display top cybersecurity subject (Light cyber landscape)
- Logs easy to integrate in a SIEM (verified on Splunk and Graylog)
- View the latest CVE and latest news related to cyber security are published
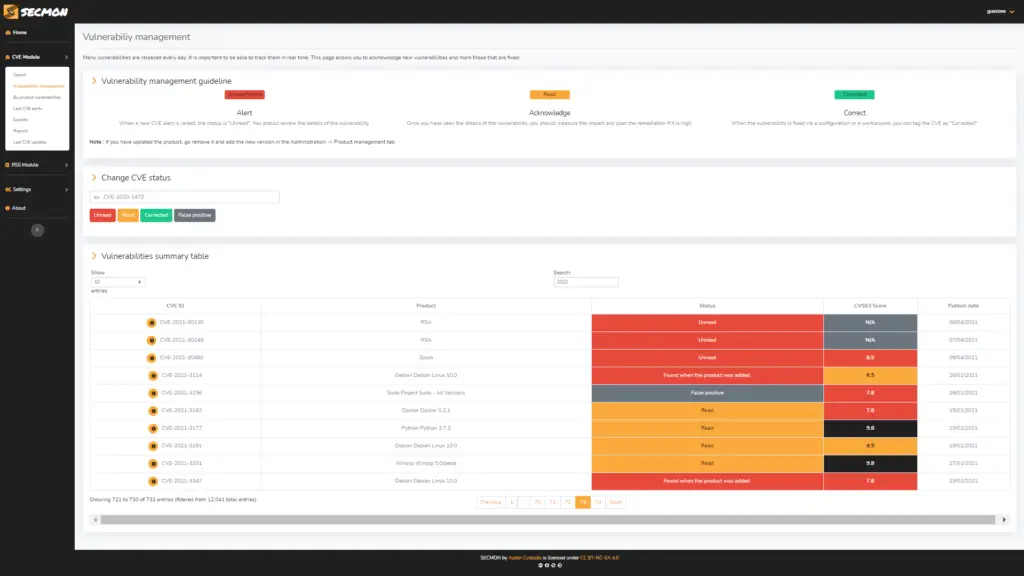
- Assign a buffer of management status of a CVE
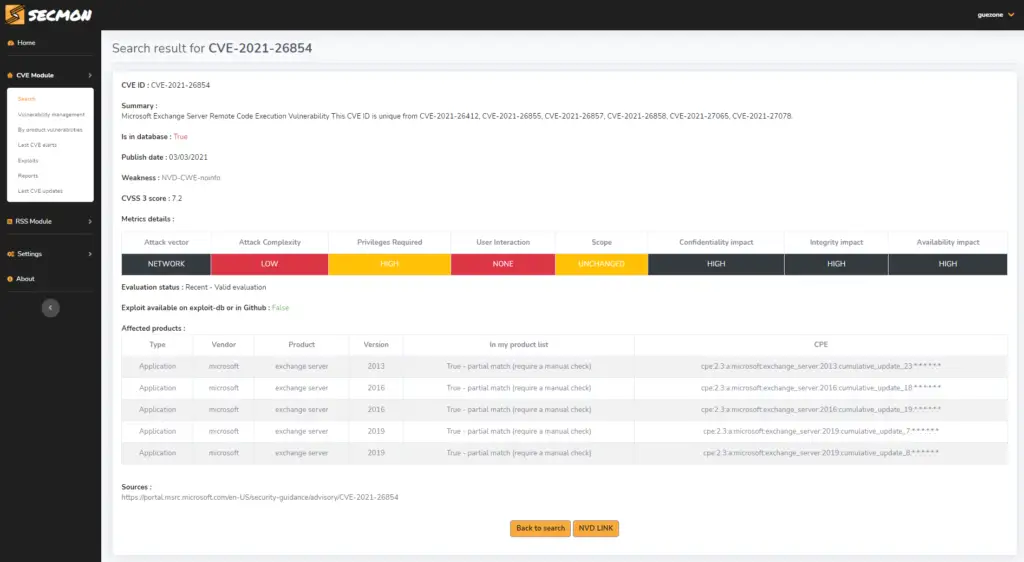
- Search all the details of a CVE
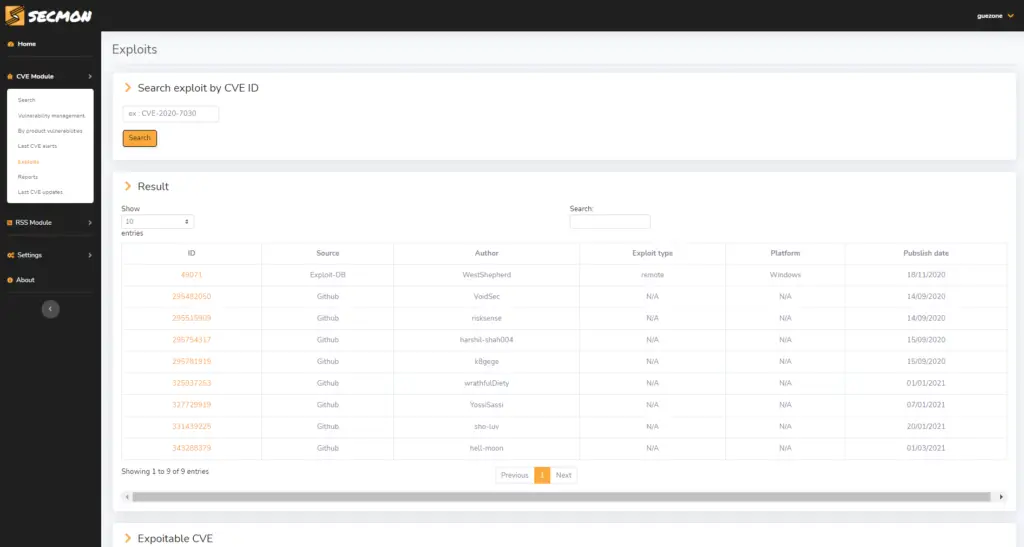
- Check if there is an exploit on Github or Exploit-DB concerning a CVE
- Search for vulnerabilities for a specified product
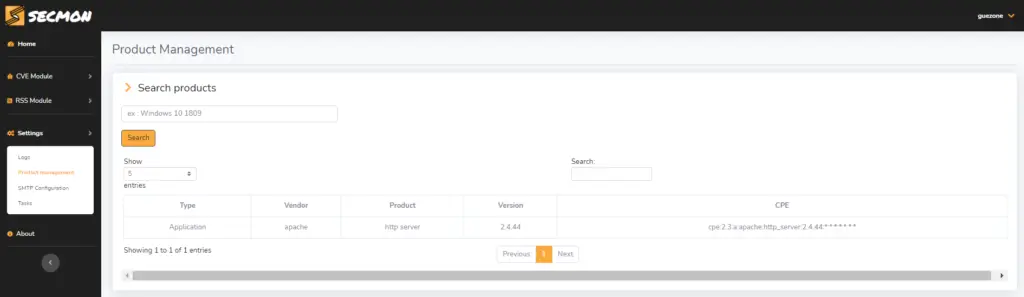
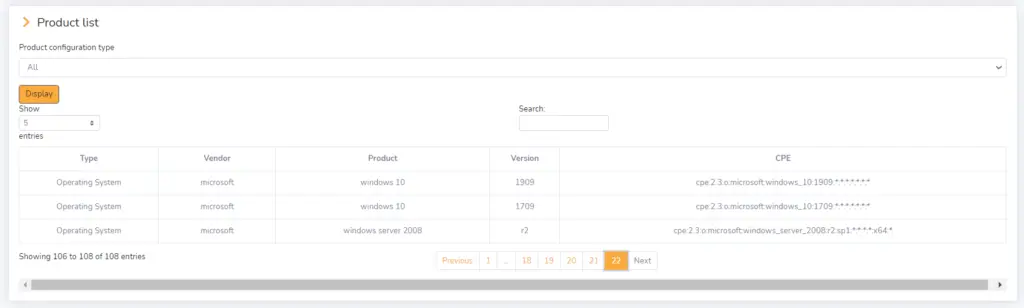
- Manage your product list: search/add/delete a product, display your referenced product list
- Monitor the sources used by pollers
Email alerts can be sent in English or French. SECMON web UI now support multi user account.
CVE are polled using two methods of collection/correspondence:
- Keyword-based : allows you to be proactive on the retrieval of CVE by leaving a little bit of precision (no version check, just word matching) on the affected products (ex: “VMWare”, “Apache”).
- CPE based (Common Platform Enumeration) : allows the retrieval of CVE that only concern the product version entered (e.g. “Windows 10 1909”, “Apache 2.4.38”)
Requirements
SECMON requires registration on Github API for exploits retrieval. It also requires :
- OS : Linux-based system (tested on Debian 10)
- Environnement : Python 3 (tested on Python 3.9 and Python 3.8)
WARNING : Web UI credentials are hashed (SHA512 with salt), on the other hand, the Github API connection credentials and the application session key are neither encrypted nor hashed. All data is stored in an unencrypted sqlite database. A few advices :
- Allow access to this machine only to persons who are authorized to do so.
- Isolate the host machine from the rest.
- Use a dedicated server/VM or Docker container.
Some screenshots
Installation
https://github.com/Guezone/SECMON/blob/master/DOCS.md
License
SECMON (by Aubin Custodio – Guezone) is licensed under CC BY-NC-SA 4.0.
This license allows you to use SECMON, to improve it and to make it live by mentioning the author but without using it for commercial purposes. As the infosec watching process is quite difficult and time consuming, it should only be used to help companies and/or users to secure their IT infrastructure and to know the current cyber security world.
Changelog
2.0 :
- Modification of the log format
- Reporting method (generation via dates)
- Web UI – new boostrap template
- Work on the Docker automation part
2.1 :
- Add a multi-user support on Web UI
- Improved auto docker configuration (to improve updates with git and volume)
- Added a Cyber Threats section that highlights the top cyber topics reported in the RSS module
- Update of README and DOCS (docker, update & screenshots part)
- Prioritisation of the CPE polling method over the keyword method
Roadmap
- Automate the deployment with docker
- First security auditing (front-end only)
- Create script to allow CPE scanning on Windows and Linux based system
- Add new sources of cyber-news
- Write user documentation for the Web UI
- Create a REST API for calling in other applications
- Write the logs in a standard format and plan to send them to a third party of SIEM type.
- Send CVE daily update report (new high risk product, CVSS changes, affected product changes, new exploitable CVE)

























Leave a Reply