


Overview
Sooty is a tool developed with the task of aiding SOC analysts with automating part of their workflow. One of the goals of Sooty is to perform as many of the routine checks as possible, allowing the analyst more time to spend on deeper analysis within the same time-frame. Details for many of Sooty’s features can be found below.
Sooty is now proudly supported by Tines.io! The SOAR Platform for Enterprise Security Teams.
Sooty can Currently:
- Sanitise URL’s to be safe to send in emails
- Perform reverse DNS and DNS lookups
- Perform reputation checks from:
- Identify if an address is potentially malicious, used for spam, web bots:
- Check if an IP address is a TOR exit node
- Decode Proofpoint URL’s, UTF-8 encoded URLS, Office SafeLink URL’s, Base64 Strings and Cisco7 Passwords.
- Get file hashes and compare them against VirusTotal (see requirements)
- Perform WhoIs Lookups
- Check Usernames and Emails against HaveIBeenPwned to see if a breach has occurred. (see requirements)
- Simple analysis of emails to retrieve URL’s, emails and header information.
- Extract IP addresses from emails.
- Unshorten URL’s that have been shortened by external services. (Limited to 10 requests per hour)
- Query URLScan.io for reputation reports.
- Analyze email addresses for known malicious activity and report on domain reputation utilising EmailRep.io
- Create dynamic email templates that can be used as a base for phishing triage response.(.msg only, .eml coming in future update)
- Perform analysis enrichment on phishing mails using the HaveIBeenPwned database, and can identify if an email address has been compromised in the past, when it happened and where the breach occurred. (Requires API Key).
- Submit URL’s to PhishTank. (see requirements)
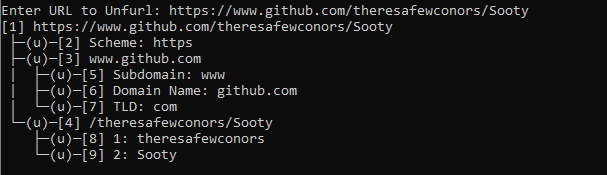
- Unfurl URL’s via the CLI version of Unfurl.
- See below for a full list and layout of currently available tools:
└── Main Menu ├── Sanitize URL's for use in emails | └── URL Sanitizing Tool ├── Decoders | ├── ProofPoint Decoder | ├── URL Decoder | ├── Office Safelinks Decoder | ├── URL Unshortener | ├── Base 64 Decoder | ├── Cisco Password 7 Decoder | └── Unfurl URL ├── Reputation Checker | └── Reputation Checker for IP's, URL's or email addresses ├── DNS Tools | ├── Reverse DNS Lookup | ├── DNS Lookup | └── WhoIs Lookup ├── Hashing Functions | ├── Hash a File | ├── Hash a Text Input | ├── Check a hash for known malicious activity | └── Hash a file and check for known malicious activity ├── Phishing Analysis | ├── Analyze an Email | ├── Analyze an email address for known malicious activity | ├── Generate an email template based on analysis | ├── Analyze a URL with Phishtank | └── HaveIBeenPwned Lookup ├── URL Scan | └── URLScan.io lookup ├── Extra's | ├── About | ├── Contributors | ├── Version | ├── Wiki | └── Github Repo └── Exit
Requirements and Installation
- Python 3.x
- Install all dependencies from the requirements.txt file.
pip install -r requirements.txt - Launch the tool by navigating to the main directory, and executing with
python Sooty.py, or simplySooty.py - Several API Keys are required to have full functionality with Sooty. However, it will still function without these keys, just without the added functionality they provide. Links are found below:
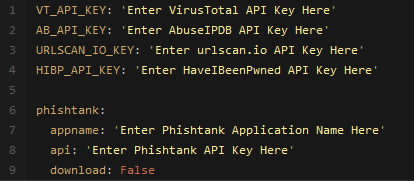
- Replace the corresponding key in the
example_config.yamlfile, and rename the file toconfig.yaml, example layout below: - For PhishTank support, an unique app name is also required as an additional field. Simply update the
config.yamlfile with your unique name.
Launch with Docker
- docker build -t sooty . && docker run –rm -it sooty
Development
Want to contribute? Great!
Code Contributions
- If you wish to work on a feature, leave a comment on the issue page and I will assign you to it.
- Under the projects tab is a list of features that are waiting to be started / completed.
- All code modifications, enhancements or additions must be done through a pull request.
- Once reviewed and merged, contributors will be added to the ReadMe.
Found a Bug? Show Me!
Bugs and Issues
- If an issue / bug is found, please open a ticket in the issue tracker and use the bug report template. Fill in this template and include any additional relevant information.
- If you wish to work on a known bug, leave a comment on the issue page and open a Pull Request to track progress. I will assign you to it.
- If there is an issue with installation or usage, use the supplied template and I will respond ASAP.
Requesting Features
- New features / requests should start by opening an issue. Please use the accompanying template when creating a new issue. This helps track new features and prevent crossover. Attach any additional info that seems relevant if necessary. Before creating a new issue, please check the Projects Tab to see if this issue has already been requested, or directly with the other open issues.
Changelog
Version 1.3 – The Templating Update
- Added first iteration of dynamic email templates that generate based on Sooty’s analysis, example below:
- Docker Image added
- Unfurl added
Version 1.2 – The Phishing Update
- Added first iteration of the Phishing tool.
- Able to analyze an email (outlook / .msg only tested at the moment) and retrieve emails, urls (Proofpoint decode if necessary) and extract info from headers.
- Extract IP’s from body of email.
- Reputation check on sender of email, and provide enriched information.
Version 1.1 – The Reputation Update
- Improved Rep Checker
- Added HaveIBeenPwned Functionality
- Added DNS Tools and WhoIs Functionality
- Added Hash and VirusTotal Checkers
- Added Abuse IPDB, Tor Exit Node, BadIP’s to Reputation Checker
Version 1.0
- Initial Release
- URL and Proofpoint Decoder
- Initial implementation of Reputation Checker
- Sanitize links to be safe for email
Roadmap
This is an outline of what features will be coming in future versions.
Version 1.2 – The Phishing Update
- Scan email attachments for malicious content, macros, files, scan hashes, etc.
Version 1.3 – The Templating Update
Add dynamic email templates that generate based on Sooty’s analysis.Edit: Added- Verify MX Records
- Perform DKIM Verification
Version 1.4 – The PCAP Analysis Update
- Add ability to analyze .pcap files and provide concise, enriched information.
Version 1.x – The Case Update
- Add a ‘New Case’ Feature, allowing output of the tool to be output to a txt file.
Contributors:
Code Contributions:
- Aaron J Copley for his modified version of ProofPoint’s code to decode ProofPoint URL’s
- James Duarte for adding a hash and auto-check option to the hashing function
- mrpnkt for adding the missing whois requirement to requirements.txt
- Gurulhu for adding the Base64 Decoder to the Decoders menu.
- AndThenEnteredAlex for adding the URLScan Function from URLScan.io
- Eric Kelson for fixing pywin32 requirement not necessary on Linux systems in requirements.txt.
- Jenetiks for removing and tidying up duplicate imports that had accumulated over time, and for providing a toggle between public and private scans on URLScan.io
- Nikosch86 for fixing an issue with hexdigest not correctly storing a file hash.
- Naveci for numerous bug fixes, QoL improvements, Cisco 7 Password Decoding, and introduced a workflow to helps with issues in future. Phishtank support has now also been added, and additional IP blacklists for the reputation checker.
- MrMeeseeks2014 fox fixing a bug relating to hash uploads.
- mrn42 for adding Docker Support.
- Ryan Benson for adding Unfurl support to the decoders section.
- Nitin Mukesh identified and fixed a bug with the BadIP’s reputation lookup, and creating a stored txt output of Sooty’s analysis.
- Sarthak for fixing an issue related to the emailrep API key.
- Lesander who fixed an issue with bash not recognizing Sooty as an executable file.
Documentation Contributors:
- Danielf-5 for improvements in the readability
- Paralax for fixing typo’s in the readme.
- mrn42 for adding Docker documentation to the readme

























Leave a Reply