
Kali Linux and Raspberry Pi for Security Analytics
As of 2020, we all are aware of the security breaches happening to the data within the organization. The organizations are using the LAN network or wifi networks, allowing the employees to access and perform their tasks and operations. To ensure that the organization’s sensitive data is secured, a secured wifi network is necessary. The term Wireless Penetration Testing has then come up to test the wifi networks if they are secure or not using some strategies and methodologies. To gain an in-depth knowledge on the approaches used for penetration testing and Kali Linux, you can undergo a Linux certification training which helps you in nurturing yourself.
The primary focus would be on the exploitation of the vulnerabilities on the wireless gateway. It is important to select the right partner to perform wireless penetration testing. The wireless penetration testing is becoming popular because of the tasks and goals that it aims for. It provides us with a report that helps us understand the data security in the organization. It gives us a clear picture of the data vulnerabilities leading to security threats, helps us in identifying if the network connection is secure or not, gives an analysis to the organization if anything is found to be weak, and has to be modified before it goes wrong. In this blog, we will understand about Kali and Raspberry Pi and their usage in Wireless Penetration Testing.
What is Kali Linux and why is it used?
Kali Linux is a free operating system that is designed to perform penetration testing and safety analysis. Formerly known as BackTrack, Kali Linux is a forensic and security-based distribution. Kali Linux is a combination of 600 Kali Linux tools that allow to perform all the different operations at one place.
It is commonly called as Kali, a platform for penetration testing designed and developed for security assessments, threats, breaches of security, etc. Kali is used by the security professionals and attackers. Kali is used by providing scalability, support and stability as it offers its extensive support.
What is Raspberry Pi and Why is it used?
Raspberry Pi is often considered as the next level of Linux. Raspberry Pi is defined as a low-level credit card device or a computing system that can be integrated with the monitor. It is usually a small device that is plugged into the monitor using an HDMI ( High Definition Multimedia Interface) cable. Raspberry Pi is one of the latest platforms that is used for penetration testing. Though it has to be purchased, it is cheaper and available to all kinds of individuals. Raspberry Pi is used as they are small in size, often called a microcomputer, with all the hardware supported accessories making it more flexible and feasible in penetration testing.
Usage of Kali Linux and Raspberry Pi in Penetration testing:
Kali Linux and Raspberry Pi are incredibly the best penetration testing platforms that allow professionals to save the organization from security breaches, attacks, etc. Kali Linux has many tools inside it.These tools are used to conduct the wifi network security assessments and evaluations to understand and check how the networks are protected.
As tools are included in Kali Linux, these tools will be used by security professionals and researchers, which will help to perform penetration testing in following methodologies and strategies. Let’s have a quick review of the popular tools that help in extensive testing of penetration.
Kismet Wireless
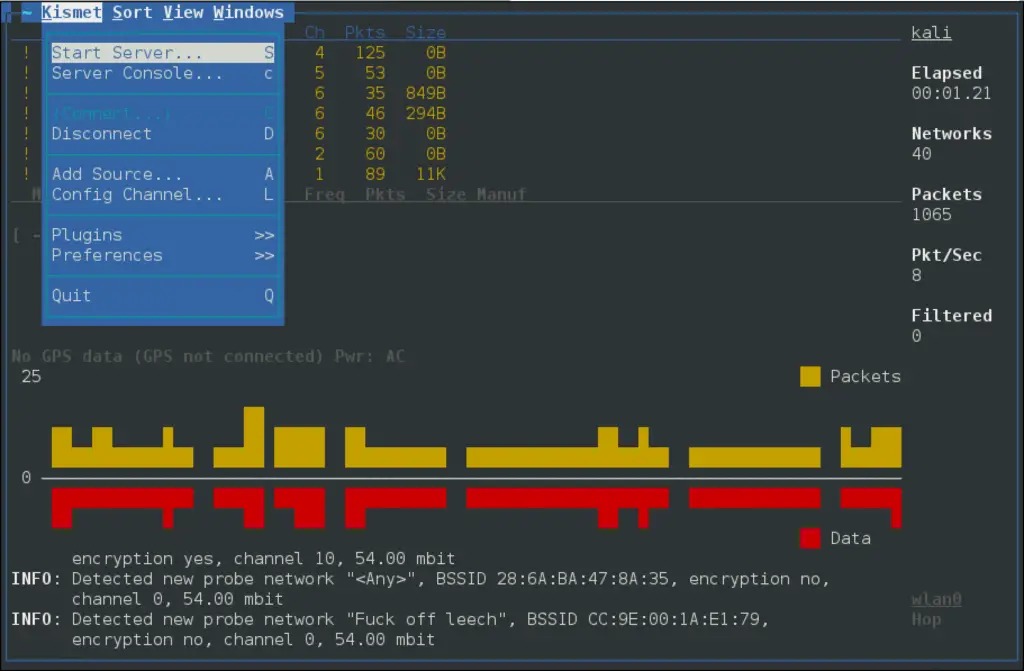
Kismet wireless is one of the most commonly used tools in Kali Linux to perform wireless penetration testing. Kismet Wireless is a multi-platform Wireless LAN Analyser designed and developed to implement all the security features like network detection, intrusion detection, packet sniffing, etc. It is developed with a compatible to work with a wireless card supporting all the different wireless networks like 802.11a, 802.11b, 802.11g, and 802.11n standard based.
Features:
- Flexible to handle and record the network logs, often called as Network logging.
- Provides its extensive support for channel hopping
- Developed with the ability and compatibility to run in a passive mode
- Helps in detecting the wireless clients and access points
- Kismet wireless helps in the detection of intrusions at a larger scale.
Aircrack-ng:
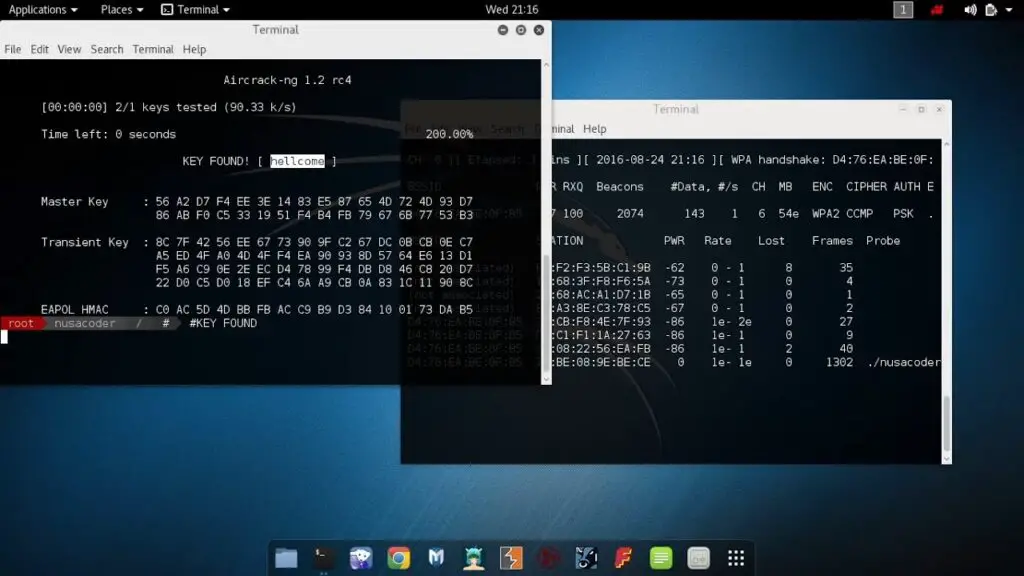
Aircrack-ng is a software security suite designed and developed with the set of tools to perform the testing of the networks in a highly scalable and compatible way. The software tools help in the detection of insecure networks, threats, packet sniffing, intrusions, etc. It helps in the monitoring of the transmission of the packets in an organized format and hence called organized packet analyzer. This software has come up with the auditing apparatus that every security professional would follow and run their analysis to detect the networks. Let us also know the apparatus that they use to perform security analytics.
Features:
- Provides its extensive support to all the different standard passwords like WEP, WPA/WPA2-PSK passwords
- Helps in packet sniffing
- It is developed with the ability to create a virtual tunnel.
- It is designed with the feature of password list management, allowing to manage the different passwords.
- It helps in faster WEP and WPA password decryption.

























Leave a Reply