

Top 10 Network Security Courses To Boost Your Career
We live in an era of technology where data has become the most influential key factor that can change the game anytime. But networking plays the most important role in maintaining the day-by-day operation when transferring the data from one place to another. It is essential to protect data from being theft or from becoming the victim of sabotage or hacking. Otherwise, any organization may incur a severe loss and fall back in the competition. Besides, the prevention of lagging and reducing the downtime also come with it. If you want to know more and learn to protect data, enroll in one of the best Network Security Courses we will mention below.
Best Network Security Courses
We have created a list that contains the best Network Security Courses available out there in this article. Any of these courses can play the role of a guide to help you protect your intellectual property and keep your company on the right track.
1. IT Fundamentals for Cybersecurity Specialization
This course is offered by IBM and available to enroll in Coursera. It is designed to prepare you for the job market and make you a powerful candidate for any certification exam. It also comes with a comprehensive assessment test to judge your skills and validate expertise through a certificate.
Insights of this course
- Suitable for beginners and starts from the fundamentals while understanding how the security-based historical events have been evolved.
- You will get an opportunity to explore Cybersecurity’s great functionalities, where the concepts of CIA Triad, access management, and incident responses will be shared.
- Other related topics, such as tools and processes, system administration, operating systems, and database vulnerabilities of Cybersecurity, will be highlighted.
- Various networking attacks and the tools that protect from these attacks like firewall, anti-virus, penetration testing, and digital forensics will be discussed.
- You will need to build a project to represent what you have learned at the end of the course to get the certificate, which you can add to your portfolio.
- Information Security, IBM New Collar, Malware. Network Security, SQL Injection, Operation Centre Analysis will be highly emphasized throughout the course.
2. Introduction to Network Security
It is one of the best Network Security Courses to get your specialization done in the most advanced network protection technology and methods. This course has already got the attention of many people with its contents, and the top rating backs its teaching style and impact on the future after completing the course.
Insights of this course
- Although this course is to become a pro, it is intended for any people interested and who want to know about cybersecurity and how it works.
- Designed to provide a deeper understanding of network security, and you will also learn to connect the cybersecurity solutions with the existing businesses.
- Students will be able to identify the network vulnerabilities and the tools that will be best to work with for generating the solution to the error.
- Understand the difference between the various security features while their pro and cons, how to use, and where to use will be covered in this course.
- Learn the best practices in the network security field to become a valuable asset in your organization for handling defense system scenarios.
- Risk Assessment, Information Security, Denial-Of-Service Attack. Public-Key Cryptography will be discussed alongside Cyber Defense and Cyber Attacks.
3. IBM Cybersecurity Analyst Professional Certificate
This course will help you to become a job-ready cybersecurity analyst and IT security analyst after completion. The beginners and the professionals looking to switch careers can take this course as a guideline to pursue their goals. It will take up to 8months to complete this course.
Insights of this course
- This course focuses on clearing the fundamentals first to make all the students comfortable before advancing to the complex concepts.
- It offers a step-by-step guideline to introduce the tools required to analyze security like data and endpoint protection, SIEM, systems, and network fundamentals.
- It comes with real-world cybersecurity scenarios and challenges to enable you to take necessary actions as incident responses or forensics accordingly.
- Gain an in-depth understanding of key compliance standards and how we can face the threat challenges with intelligence will be taught as well.
- Covers a wide range of topics, including Malware, Cybersecurity, Cyber Attacks, database vulnerabilities, Network Security, and SQL Injection.
- Develop your skills with industry-specific tools like Wireshark, IBM QRadar, IBM MaaS360, IBM Guardium, IBM Resilient, i2 Enterprise Insight Analysis, and so on.
4. Networking and Security Architecture with VMware NSX
This one is the best among the network security courses when it comes to network virtualization with VMware NSX. This 8 weeks course is designed to provide an overview of network security architecture, the business value of NSx, and the best cases where we can use NSX.
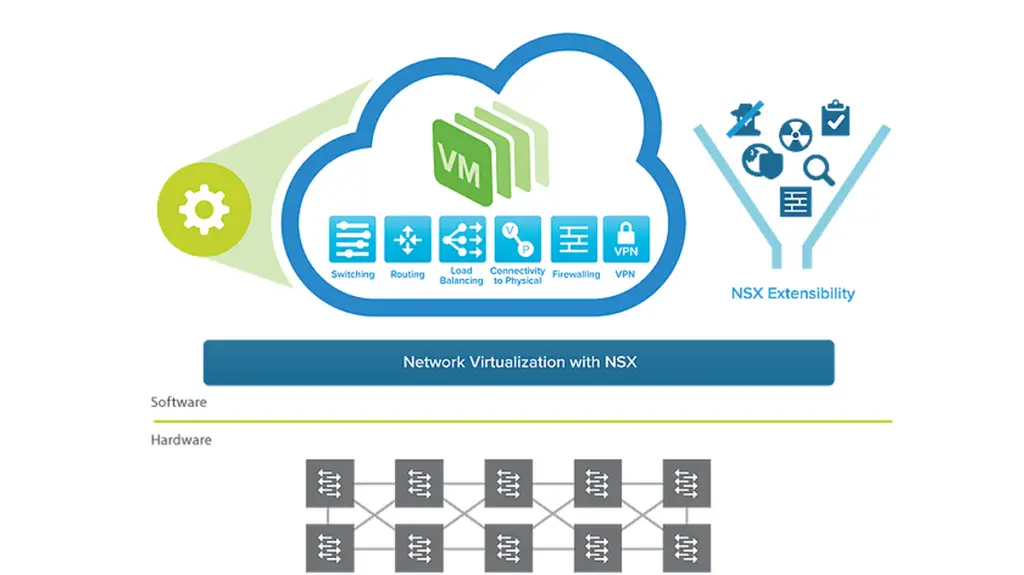
Insights of this course
- Introduces the security solution architecture, and you will understand the difference between traditional networking tools and VMware NSx.
- To make you understand NSx better Micro-segmentation functions, automation with OpenStack and vRealize will be covered.
- Besides, how to recover from the disasters and integrate with business continuity will be discussed alongside how to start the operational transformation.
- It has included the demonstration of hands-on experience to develop the learning plan. You will gain knowledge of Multi-site Networking and Security.
- Students will get the opportunity to get Multi-site Solutions with VMware NSX Demo and configure a custom network using the application continuity solutions.
- Explore the use cases of Cross-vCenter NSX, Key Concepts, application behavior monitoring, and the integration of NSx with any ecosystem that will be emphasized.
5. Real-Time Network Threat Detection and Mitigation
This course is offered by the Tandon School of Engineering and available in Coursera. You can enroll in this course anytime, and the deadlines are also flexible. So even you are a working professional, you can complete this course and meet your desired goals. You will also get a certificate after completing the course successfully.
Insights of this course
- A wide range of security functions is discussed elaborately in this course to discuss the cybersecurity tools in terms of TCP/IP protocol.
- Some of the basic TCP/IP security hacks will be introduced alongside other network security solutions, which include stateless and stateful firewalls, and so on.
- Learn to build and configure firewalls of packet filters and proxies type so that you can help any organization by protecting enterprise-level intellectual assets.
- Understand the enterprise network security by learning Large Government Agency Attack, Layer 3 DDOS Protection, and Layer 7 Application Level DDOS Risk.
- Alongside, APT Schema Through Perimeter Holes, Third-Party Security, Target APT Attack, and Financial Website DDOS Attacks will be discussed in detail.
- Besides, learn to manage by exception, systematic auditing, detect the intrusions and behaviors, design SIEM and SOC, and IDS vs. IPS6 will be discussed.
6. Intel® Network Academy – Network Transformation 101
Intel designs this comprehensive training program, and so you can undoubtedly expect the best from it. It starts at the beginner level and then advances to the complex concepts of network security and mitigation. This course is completely online-based, while English subtitles are also included.
Insights of this course
- The beginners and the professionals looking to switch careers can try this course as the deadlines are flexible, and you can earn a certificate.
- Software-defined infrastructure (SDI) network functions, virtualization (NFV), and software-defined networking (SDN) cover the major part of this course.
- It can be referred to as a valuable collection of Intel technologies that a networking professional can use to enhance knowledge and increase efficiency.
- Industry trends, Key concepts of Intel security features, and technical aspects of NFV deployments will also be taught to improve the students’ skills.
- Get an overview of the Telco cloud, including wireless technology and spectrum, IoT licensing, market trends, AI use cases, and communications service providers.
- Discusses EPC Architecture, Virtualization, Virtual Ran, SD-WAN Deployments, Radio Access Technology, Mobile Edge Computing, FlexRAN, EPC, and vEPC.
7. Palo Alto Networks Security Specialization
The Cybersecurity academy offers this course and will help you prepare yourself for the demanding job market. At Least fifty percent of students who have completed this specialization got their desired job. Besides, it can be an ideal guide if anyone is interested in switching his/her career.
Insights of this course
- It is completely online, and you can access using any device at any time. Besides, a certificate is also offered at the end of the course, and deadlines are flexible.
- The fundamentals of cybersecurity will be discussed in detail so that students can identify the potentially mitigate attacks against any network or critical infrastructure.
- Covers the networking fundamentals like physical, logical, and virtual addressing, TCP/IP model, subnet mask, and packets’ encapsulation at specific layers.
- It is intended to enable students to examine the network security environments and expose the vulnerabilities and risk factors using the system-specific tools.
- You will learn the best practices to plan, design, implement, troubleshoot, which is required to maintain any Cisco standard network configuration.
- Adopt a wide range of security methodologies and filtering methodologies such as user, application, and content ID.
8. Security Awareness Training
It is one of the top-rated network security courses available out there. Although this course does not come with a certificate, most students still have surprised most students while their positive feedback can back this course’s popularity. It is designed by (ISC) which has a goal to build safe and secure networks worldwide.
Insights of this course
- This course is designed to raise awareness among the general people for network security and explain that it is suitable for every end-user type.
- Any organization can inspire their employee to get this course done to understand the Importance of Security, Data and Account Security, and Passwords.
- Data is the most powerful asset collected by an organization, and you will learn to protect and provide safeguards to these intellectual assets owned by your company.
- When it comes to ensuring data protection, we must know how to protect data. Learn the best practices, tips, and selective approaches to employ a strong password.
- You will learn to identify network vulnerabilities and mitigate the risks, especially when securing our mobile devices, laptops, or desktop computers.
- A wide range of malware and symptoms of malware infections will be discussed while you will get an opportunity to explore the platforms used by scammers.
9. Check Point Jump Start: Maestro Hyperscale Network Security
This great course of network security is designed to ensure you ensure the security of any Hyperscale Network. It is an intermediate-level course and offered by Check Point Software Technologies Limited. It will help you know your strengths and weaknesses to judge yourself before applying for a job.
Insights of this course
- You will discover the basic concepts of Hyperscale Network Security, where you will learn the Maestro Hyperscale Orchestrator appliances in this online course.
- Get an opportunity to explore the features and Command Line Interface of Maestro Hyperscale Orchestrator, and Single Management Object will be discussed.
- A demonstration video is included with each section to understand better while you will learn the advanced concepts of Maestro Hyperscale Orchestrator.
- How we can use the interface to construct a Maestro Security group will be shown. Real-life problems and a lot of examples are also included in this course.
- Learn the concepts of ensuring high availability using two Maestro Hyperscale Orchestrator appliances so that one can be used when another is absent.
- This is a very compact course and designed for working professionals who are already in this field. You can even complete this course within four hours only.
10. The Complete Nmap Ethical Hacking Course: Network Security
This is the best seller among the Network Security Courses available in Udemy as more than eighteen thousand people have already completed this course. It can be referred to as the best guide to becoming a pro ethical hacker while the network security tool – Nmap will be introduced.
Insights of this course
- Explore the features and functions of the NMap security tool used for ethical hacking and get your desired job in system administration and network security.
- Networking will be discussed in the context of NMap throughout the course so that you can discover the secrets of Ethical Hacking.
- Port Scanning and Fingerprinting will be discussed, and Nmap Basics, Nmap Target Specification, Nmap Port states, Cloud-Based Hacking, and so on.
- Nmap discovery is highly emphasized alongside Ping Scanning and Nmap Scripting Engine, where Categories, its usage and cool scripts, and writing scripts are included.
- Nmap scanning techniques will be covered where you will learn SYN and Connect, UDP and SCTP, TCP ACK, NULL, FIN, Xmas, Maimon Idle Scan, and IP Protocol.
- Concepts of Spoofing, Timing and Performance, Output & Miscellaneous Options, Command and Control Hacking Bypassing firewalls are also highlighted.
Finally
Network security is how a network can be protected from misuse, malware, illegal access, modification, or any other unethical action. In the coming future, the IoT or the Internet of Things will be the next big thing, so network vulnerabilities are expected to rise at a large number.

























Leave a Reply