
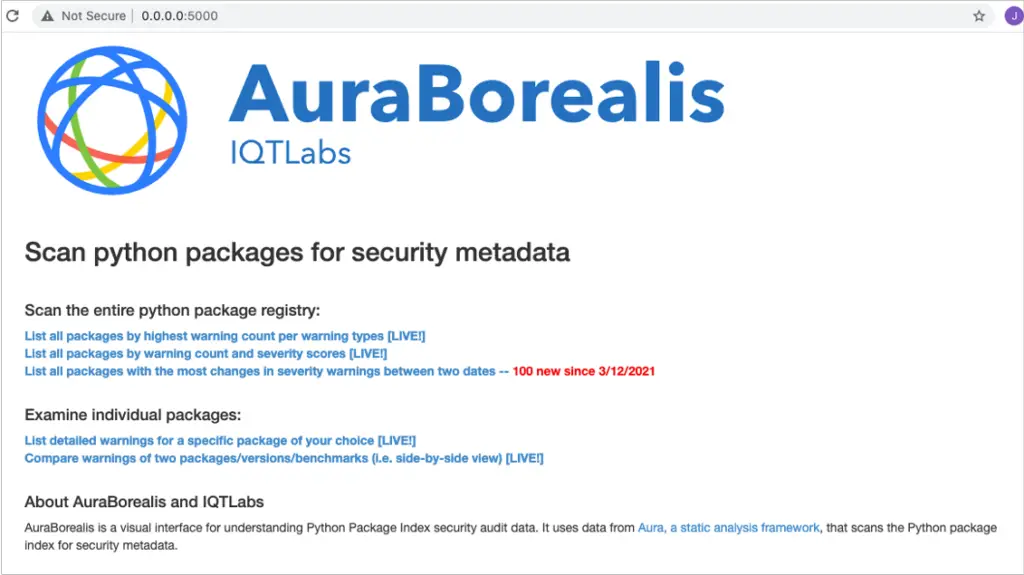
Do You Know What’s In Your Python Packages? A Tool for Visualizing Python Package Registry Security Audit Data
About
AuraBorealis is a web application for visualizing anomalous and potentially malicious code in Python package registries. It uses security audit data produced by scanning the Python Package Index (PyPI) via Aura, a static analysis designed for large scale security auditing of Python packages. The current tool is a proof-of-concept, and includes some live Aura data, as well as some mockup data for demo purposes.
Current features include:
- Scanning the entire python package registry to:
- List packages with the highest number of security warnings, sorted by Aura warning type
- List packages sorted by the total and unique count of warnings
- List packages by their overall severity score
- Displaying security warnings for an individual package, sorted by criticality
- Visualize the line numbers and lines of code in files generating security warnings for a specific package
- Compare two packages for security warnings
Instructions
Turn on your VPN (at IQT)
Clone the repository.
git clone https://github.com/IQTLabs/AuraBorealisApp.git
Navigate to aura-borealis-flask-app directory.
cd aura-borealis-flask-app
Install dependencies.
pip install -r requirements.txt
Run the app.
python app.py
Navigate to the URL http://0.0.0.0:7000/ via a browser.
Feature Roadmap
- Compare a package to a benchmark profile of packages of similar purpose for security warnings
- Compare different versions of the same package for security warnings
- List packages that have changes in their warnings and/or severity score between two dates
- Ability to scan an internal package/registry that’s not public on PyPI
- Display an analysis of permissions (does this package make a network connection? Does this package require OS-level library permissions?)
Contact Information
jmeyers@iqt.org (John Speed Meyers, IQT Labs, Secure Code Reuse project lead).
The lead developer and creator of Aura is Martin Carnogusky of sourcecode.ai.
Related Work
- IQT blog post on secure code reuse
- IQT blog posts on typosquatting and preventing typosquatting via pypi-scan
- USENIX article on “Counting Broken Links: A Quant’s View of Software Supply Chain Security”
- IQT open source dataset on known software supply chain compromises
























Leave a Reply